Researchers Find Significant Vulnerabilities in macOS Privacy Protections
Attacks require executing code on a system but foil Apple's approach to protecting private data and systems files.
August 5, 2021

BLACK HAT USA 2021 - Applications that are allowed to run on Apple's operating system, macOS, can exceed the permissions granted to them by the user and the operation system, allowing a variety of privacy attacks, such as grabbing address book information, taking screenshots, and gaining access to system files, two researchers stated at a Black Hat USA briefing on Aug. 4.
The researchers — Csaba Fitzl with Offensive Security and Wojciech Regula with SecuRing — found more than a score of vulnerabilities and insecure configurations that allowed the duo to bypass the core mechanism for protecting user privacy — Apple's Transparency, Consent, and Control (TCC) privacy framework. The researchers used malicious plug-ins and process injection into third-party applications — among other approaches — to attack the TCC daemon and give their proof-of-concept attack full permissions on the system.
The two researchers reported the issues to Apple and many of them have been fixed. However, the security weaknesses are not just Apple's problem but also represent issues that third-party software makers need to fix, said Offensive Security's Fitzl during the presentation at Black Hat USA.
"There are too many Apple binaries with exceptions to access private data, which opens up the platform for abuses," he said. "Many, many third-party applications are vulnerable to injection attacks, so if those applications have access to private resources, then those resources are vulnerable."
While the vulnerabilities are not exploitable remotely by themselves, similar issues have been used by attackers to bypass system protections on sensitive data. By convincing the user to run code on their system, the vulnerabilities can be exploited to bypass much of the data security built into Apple's macOS, iOS, and tvOS.
In May, Apple fixed issues in its macOS and tvOS that were exploited in the wild, allowing a malware program, known as XCSSET, to take screenshots and grab Safari browser cookies without requiring user permission. Bypassing privacy permissions on Apple's operation systems has become increasingly popular, as the typical permission request to the user through a dialog box will often tip them off to malware running on the system.
However, bypassing TCC is not a skeleton key to the system. Ransomware, for example, will not be able to encrypt system files following a TCC bypass — the attacker needs to do more, said SecuRing's Regula.
"Ransomware cannot encrypt privacy protected files because they are not only read protected, but write protected," he said.
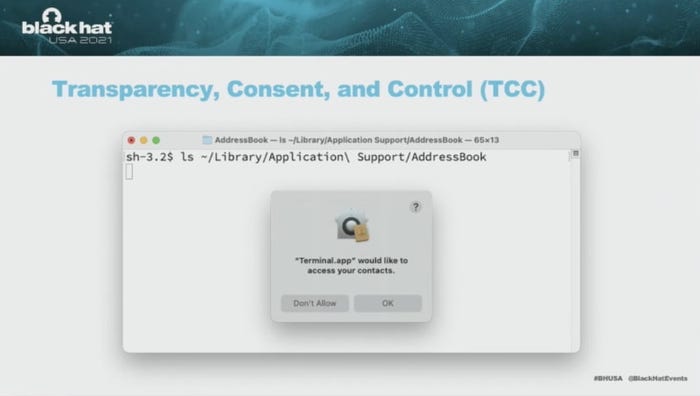
Security for macOS is based on the System Integrity Protection (SIP) framework, which restricts access to many of the directories, even from a user with root privileges. TCC is based on SIP and provides the mechanism for protecting private data from access. Users interact with the TCC when they use privacy controls found in the Security & Privacy tab of the System Preferences control panel or when a permissions dialog box appears because an application wants to access private data or a private feature, such as the camera.
"TCC limits access to certain data, so that, for example, a malicious application cannot access your desktop or your address book," Regula said during the presentation.
The researchers discovered a variety of ways to gain access to applications or features that have the capability to make TCC changes, and through that method make their own malicious changes to permissions.
In one attack chain, the researchers used a malicious plug-in for the macOS Directory Utility, which keeps track of the user's home directory information, NFSHomeDirectory, to inject code into the process and update the TCC database with fake permissions. In another attack chain, the researchers found a variety of vulnerable system and third-party applications with permissions to change the TCC database and used process injection to change permissions and entitlements.
While the researchers described the issue using the XSAN utility, xsanctl, third-party applications — such as Firefox, Signal, and SnagIt — also had the weakness. The developers of the latter two applications have fixed the issues.
"This group of vulnerabilities is especially problematic because a lot of third-party applications are vulnerable to process injection techniques," Regula said. "So if you download a third-party application to your Mac and you give it TCC permissions, you have to be aware that malware can abuse that application."
While Apple took significant time to fix the issues — or even confirm the issues, requiring up to half a year in some cases — the company has made good on its promises of a bounty for such issues, Regula said.
"Apple pays what is promised," he said. "But bug fixes are often slow, especially if it is more of a design issue. [For example,] some bugs won't be fixed until Monterey."
Read more about:
Black Hat NewsAbout the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




