Kaspersky: Lazarus Takes Aim at macOS in Cryptocurrency Campaign
Kaspersky researchers said users of Apple and Linux systems should see the AppleJesus campaign as a warning not to get lax in their cybersecurity efforts.

The notorious Lazarus cybercriminal organization, long suspected of being sponsored by North Korea, is back with another campaign that reuses an older malware tool but expands the group's reach beyond just Windows systems and into machines running Apple's macOS operating system, according to researchers with Kaspersky Lab.
The campaign, which the analysts have dubbed "AppleJesus," would be the first time that Lazarus was seen targeting macOS systems. There also is a version of the Trojan malware for Windows machines, and according to Kurt Baumgartner, principal security researcher at Kaspersky, there is another version for Linux systems in the works.
The AppleJesus campaign should serve as a warning to users of Linux and Apple systems that they can't get lax in their security efforts simply because Windows remain the top target of threat actors, Bumgartner told Security Now in an email.
"We have seen multiple other Russian-speaking, Chinese-speaking, and other APT [advanced persistent threat] targeting macOS and iOS, in some cases for years now," he said. "Clearly, there is interest in developing and maintaining MacOS and iOS implants from groups like these, but still not with the same intensity and focus as Windows malware. MacOS users can't blindly trust software and install it. The attackers stated that a variant supporting Linux will be 'coming soon,' and we have to restate the same message to Linux users as well -- you cannot blindly trust software, even when it appears to come from a legitimate source."

PIRO4D/Pixabay
According to the Kaspersky researchers, the AppleJesus malware fits in with past efforts by Lazarus to operate campaigns to steal money. The highly active group -- which also has run cyberespionage and cyberstabotage campaigns -- has targeted financial institutions. In the past several months, it has attacked several banks, financial tech companies and global cryptocurrency exchanges, they said. (See North Korea Stole 'Billions' in Cryptocurrency Heist, Official Claims.)
In this case, Kaspersky analysts discovered AppleJesus while investigating an attack on a cryptocurrency exchange in Asia. The exchange was infected via a malicious cryptocurrency trading application that came to the company through a recommendation over email.
"It turned out that an unsuspecting employee of the company had willingly downloaded a third-party application from a legitimate looking website and their computer had been infected with malware known as Fallchill, an old tool that Lazarus has recently switched back to," the analysts said in a blog post.
The appearance of FallChill gave researchers the ability to point attribution for the attack at Lazarus. Reuse of code by cybercriminals is not uncommon, and there had been a number of reports -- including an alert from US-CERT -- that Fallchill was back in use. A recent report by researchers at McAfee and Intezer found high rates of code re-use among threat groups linked with North Korea. (See Researchers Show That Code Reuse Links Various North Korean Malware Groups.)
The threat actors invested a lot of time and effort to hide the trojanized malware from security systems, the Kaspersky analysts wrote. Rather than simply putting malicious code into distributed software that was then put onto a website, the attackers created a legitimate-looking application called Celas Trade Pro that came from a company called Celas Ltd. The application, which Kaspersky described as an all-in-one style cryptocurrency trading program developed by Celas, didn't indicate malicious behavior.
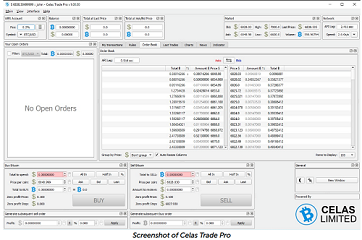
A screenshot of the legitimate-looking website that the attackers created for the campaign.
However, when the software is downloaded, it comes with an updater that is installed. In legitimate software, updaters are used to download new versions of the program. In AppleJesus, the updater runs a reconnaissance mission, collecting information about the victim's system. The data is sent back to a command-and-control server, which determines whether the system is worth attack. If so, the malicious code comes back to the system as a software update, which is when Fallchill is installed.
With Fallchill in place, the Trojan gives the attackers essentially unlimited access to the system, enabling them to steal financial information or to deploy more tools to get that job done. The functionality of the Trojan is exactly the same for both Windows and macOS systems.
The Celas Trade Pro application and the Celas website look legitimate and come with a valid SSL digital certificate for signing software and seemingly legitimate domain registration records. However, Kaspersky analysts couldn't find a legitimate business using the address given on the certificate.
"We cannot say with full certainty whether Celas LLC was compromised and the threat actor abused it to push malware through an update mechanism," they wrote in the blog. "However, the multiple successful Lazarus attempts to compromise supply chain companies suggest that it will keep exploring this infection method. From all angles, the Celas LLC story looks like the threat actor has found an elaborate way to create a legitimate looking business and inject a malicious payload into a 'legitimate looking' software update mechanism. Sounds logical: if one cannot compromise a supply chain, why not to make fake one?"
Baumgartner told Security Now that there are "many data points" to support the hypothesis that Lazarus created Celas, even if researchers can't say it with 100% certainty.
"Lazarus would not be the first APT to go to greater lengths spoofing legitimate businesses to support their own efforts," he said. "These Lazarus efforts are an ongoing extension to steal large amounts of cryptocurrency and cash from cryptocurrency exchanges and traders, banks and casinos."
Kaspersky researchers said there are a number of steps businesses should take to protect themselves against attacks like AppleJesus, including using security solutions that include malicious-behavior detection capabilities, subscribing to a threat intelligence reporting service and using multi-factor authentication and hardware wallets if dealing with significant financial transactions.
In addition, organizations should not automatically trust the code running on their systems. As AppleJesus shows, an authentic-looking website, a legitimate-looking company profile and digital certificates aren't guarantees against backdoors, they said.
Related posts:
��— Jeffrey Burt is a longtime tech journalist whose work has appeared in such publications as eWEEK, The Next Platform and Channelnomics.
Read more about:
Security NowAbout the Author
You May Also Like




