Google Cloud Aims to Share Its Vetted Open Source Ecosystem
The online giant analyzes, patches, and maintains its own versions of open source software, and now the company plans to give others access to its libraries and components as a subscription.
May 17, 2022

Developers who want to benefit from Google's security efforts will soon be able to subscribe to a service that allows developers to use open source components that they know have been vetted and patched for security issues by Google's developers.
The service, dubbed Assured Open Source Software (OSS), provides versions of popular open source packages that are scanned frequently, augmented by metadata created by code analysis, comply with the nascent Supply chain Levels for Software Artifacts (SLSA) framework, and are signed by Google.
In many ways, the service is similar to the curated Linux distributions maintained by companies such as Red Hat and Ubuntu, says Eric Brewer, vice president of infrastructure for Google Cloud and a Google Fellow.
"The idea of having curated version is not new per se, but it is just more important than ever," he says. "Plus, we wanted to show that it is important to actually do the provenance, do the metadata, do the scanning, do the fuzzing, build it from source — and sign it. That's the right way to do it."
The announcement of the new service comes a week after the Linux Foundation and the Open Software Security Foundation, along with the support of nearly 40 companies, released a plan for securing open source software. That effort is focused on 10 separate initiatives in three broad areas: securing open source production, improving vulnerability discovery and remediation, and speeding patch cadence.
While Google is a major sponsor of the effort and has provided technology and specifications for a myriad of security-focused efforts — such as Security Scorecards, AllStars, and the Alpha Omega Project — Assured OSS will be eventually be a paid, commercial service, Brewer says.
"Last week was about the community focus," Brewer says. "But you ... [also] need a lot of private investment from many different companies to make these things better, easier to use, and you also need — especially for the critical core stuff — you need a lot of industry cooperation."
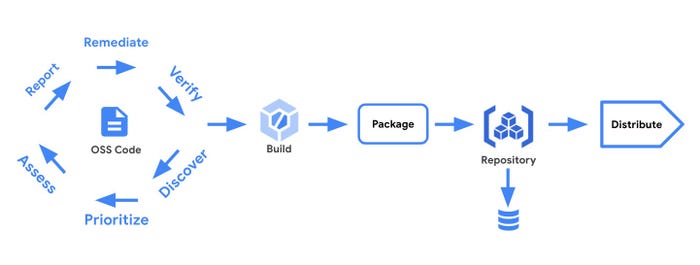
Open source software requires companies to analyze and maintain commonly used components. Source: Google Cloud blog
Scanning, Fuzzing, and Checking on 100K Cores
While most companies maintain their own package management system as a private repository, Google's level of vetting and security testing is significant, when looking at the numbers.
The company has an end-to-end process that includes continuous fuzzing of more than 500 of the most popular packages, using a massive infrastructure based on 100,000 processor cores, Google stated in a blog post announcing the Assured OSS service. The company also provides software bill of materials (SBOM) and supply chain integrity checking through the SLSA framework.
The Assured OSS framework will also natively integrate with software-security analytics firm Snyk.
"We recognize that most organizations do not have the resources or experience to construct and operate such a comprehensive program," Google Cloud stated in its blog post. "Instead, their development teams might individually decide where they get third-party source code and packages, how they are built, and how to redistribute them within their own organizations according to their goals, threat and risk model, and resources."
Overlapping Efforts Pose inefficiency Risk
Google is not alone in offering a curated collection of vetted open source software. In addition to the aforementioned Linux distros, a variety of companies — such as Anaconda — have created vetted repositories that include managing both patching and integrity issues for companies. In addition, other companies — such as Snyk, Sonotype, and Debricked — offer ways to evaluate open-source projects and libraries based on security metrics.
Google's new service raises the specter, however, that multiple companies will offer overlapping services that provide similar analyses of the top 500 packages, but do not venture into vetting packages that are less popular but still important. While redundancy is often a good attribute — because a company could find a vulnerability that another company misses — it is important for organizations to also provide more coverage across a greater number of packages, Brewer acknowledges .
"There are lots of ways to work together, but I think open source by its nature, because it is already shared, requires we work together better," he says. "So at a minimum, we should make sure that we are fixing different packages, rather than fixing the same packages — it would be globally inefficient to do that."
Assured OSS will be available to preview sometime in the third quarter of 2022, according to Google.
About the Author
You May Also Like




