End User Lockdown: Dark Reading Caption Contest Winners
Phishing, cybersecurity training, biometrics and casual Fridays. And the winners are ...
June 7, 2019
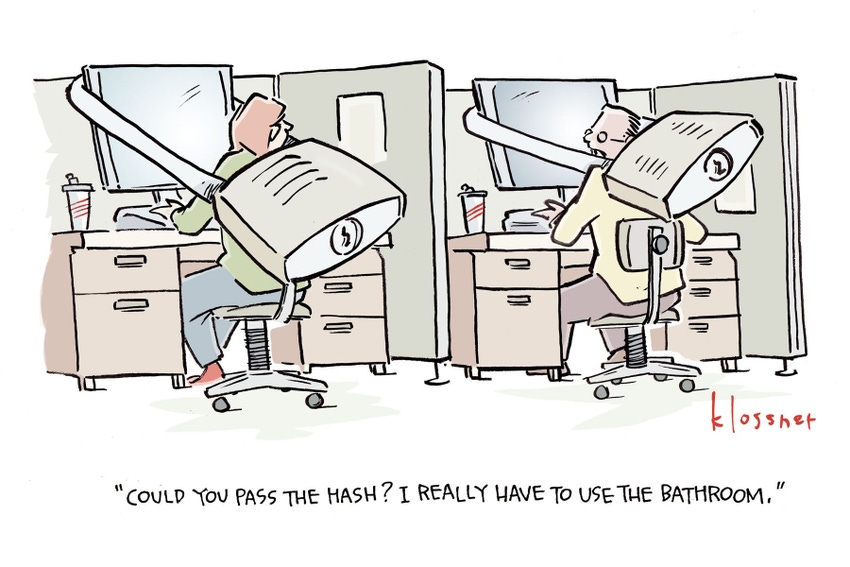
Dark Reading reader Nick Walker (aka ntwalk) earns the top honors and a $25 Amazon gift card for his password cracking play on words in the caption, penned below.
When not penning cartoon captions, Nick, of Lowell, Arkansas, works as a security analyst at J.B. Hunt Transport Services, Inc.
Coming in as a close second to win a $10 Amazon gift card is Mark Bartel, a software engineer from The Dalles, Oregon, with the clever, “I told you we needed to pass that cybersecurity training class."
Many thanks to everyone who entered the contest and to our loyal readers who cheered the contestants on. Also a shout out to our judges, John Klossner and the Dark Reading editorial team: Tim Wilson, Kelly Jackson Higgins, Sara Peters, Kelly Sheridan, Curtis Franklin, Jim Donahue, Gayle Kesten, and yours truly.
If you haven't had a chance to read all the entries, be sure to check them out today.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024