Encrypted Traffic, Once Thought Safe, Now Responsible For Most Cyberthreats
It's a classic attacker move: Use security protections against those who deploy them. But organizations can still defuse and prevent these encrypted attacks.

Once upon a time, encrypted traffic was considered the safe, secure option for browsing and doing business online. However, going back to December 2013, the Google Transparency Report shows just 48% of Web traffic was encrypted. Flash forward to today, and the volume of encrypted Web traffic is up to 95%. However, the threat landscape has changed a lot since 2013, and now we find the majority of cyberthreats lurking within encrypted channels.
Hidden in your encrypted Internet traffic layers are malware payloads, phishing scams, sensitive data leaks, and more. To understand this better, the State of Encrypted Attacks 2022 Report analyzed 24 billion threats from October 2021 to September 2022 to reveal details on threats embedded in HTTPS traffic, including SSL and TLS. The report shows a consistent upward trend of attacks using encrypted channels — from 57% in 2020 to 80% in 2021 — ultimately finding that more than 85% of attacks were encrypted in 2022. There were other major findings as well.
Most Encrypted Threats Involve Malware
While cybercriminals hide a variety of attack tactics in encrypted traffic, malware remains the most prevalent. Malicious scripts and payloads used throughout the attack sequence make up nearly 90% of the encrypted attack tactics blocked in 2022.
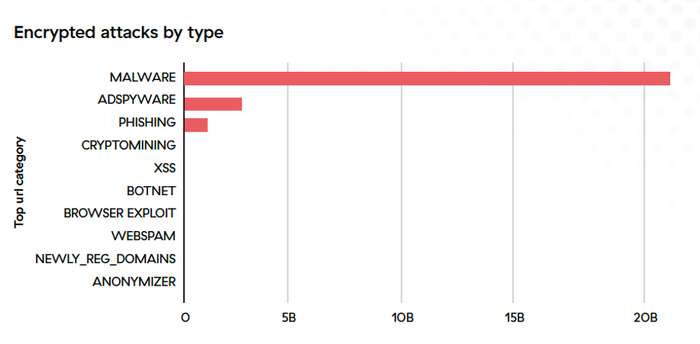
Fig. 1. Distribution of 2022 encrypted attacks. Source: Zscaler ThreatLabz
Malware continues to pose the greatest threat to individuals and businesses across nine key industries, with manufacturing, education, and healthcare the most common targets. This category includes ransomware, which remains a top concern for CISOs, as ransomware attacks have increased by 80% year over year.
The most prevalent malware families the ThreatLabz team observed abusing encrypted channels include ChromeLoader, Gamaredon, AdLoad, SolarMarker, and Manuscrypt.
US, India Are Top Targets for Encrypted Attacks
The five countries most targeted by encrypted attacks in 2022 were the US, India, South Africa, the UK, and Australia. In addition, several countries saw significant upticks in targets year over year, including Japan (+613%), the US (+155%), and India (+87%).
Encrypted Attacks Increased in Manufacturing, Education
More than doubling in encrypted attacks (239%), manufacturing displaced technology as the most targeted industry in 2022. Encrypted attacks against the education industry were also up significantly (134%). Attackers particularly favored manufacturing over other sectors as a target for ad spyware. It is also one of two industries most often phished via encrypted channels — the other being healthcare.
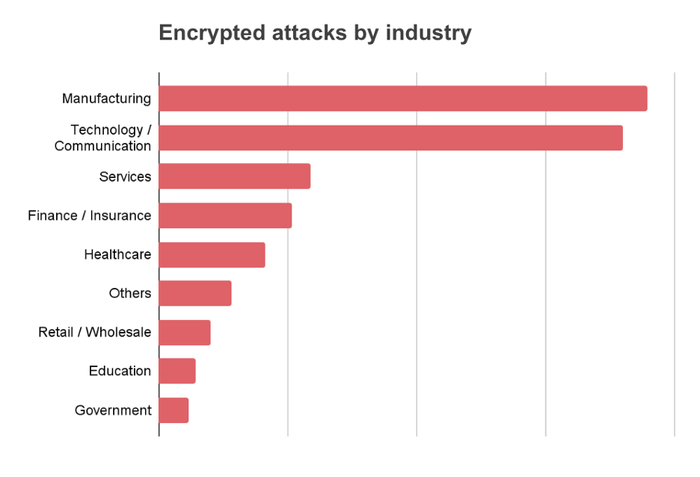
Fig. 2. Top vertical industries targeted by encrypted attacks in 2022. Source: Zscaler ThreatLabz
Today, most attacks leverage SSL or TLS encryption, which is resource-intensive to inspect at scale and best done with a cloud-native proxy architecture. While legacy firewalls support packet filtering and stateful inspection, their resource limitations make them poorly suited for this task. This creates a critical need for organizations to implement cloud-native architectures that support full inspection of encrypted traffic in alignment with zero-trust principles.
How to Protect Yourself
For defenders, the imperative is clear: all encrypted traffic must be thoroughly inspected to detect and stop cyberthreats before they cause damage. While we wait for governments, compliance frameworks, and other vendors to catch up with this reality, it will be up to defenders and leaders to raise the flag and champion initiatives to mitigate this common threat tactic. Zero-trust strategies and architectures — in which you trust nobody and inspect and authenticate everything — are the most effective way to protect your organization from encrypted attacks and other advanced threats.
Attacks start with reconnaissance and an initial compromise of an endpoint or asset exposed to the Internet. Once inside, attackers perform lateral propagation, including reconnaissance and establishing a network foothold. Finally, attackers act to achieve their objectives, which often involve data exfiltration.
Your defenses should include controls for each of those stages. Minimize the attack surface by making internal apps invisible to the Internet, and prevent compromise by using cloud-native proxy architecture to inspect all traffic inline and at scale, enforcing consistent security policies. Organizations should also stop lateral movement by connecting users directly to applications (rather than the network) to reduce the attack surface, and contain threats using deception and workload segmentation. They can also stop data loss by inspecting all Internet-bound traffic, including encrypted channels, to prevent data theft.
If you are looking to minimize the risk of encrypted attacks for your organization, consider these recommendations as part of your adoption strategy:
Use a cloud-native, proxy-based architecture to decrypt, detect, and prevent threats in all encrypted traffic at scale.
Leverage an AI-driven sandbox to quarantine unknown attacks and stop patient-zero malware.
Inspect all traffic, all the time, whether a user is at home, at headquarters, or on the go, to ensure everyone is consistently protected against encrypted threats.
Terminate every connection to allow an inline proxy architecture to inspect all traffic, including encrypted traffic, in real-time — before it reaches its destination — to prevent ransomware, malware, and more.
Protect data using granular context-based policies, verifying access requests and rights based on context.
Eliminate the attack surface by connecting users directly to the apps and resources they need, never to networks.
Read more Partner Perspectives from Zscaler.
About the Author
You May Also Like




