7 Breaches & Hacks That Throw Shade on Biometric Security
Stolen fingerprints, fake hands, voice synthetization, and other nefarious techniques show biometrics has plenty of challenges.
August 30, 2019
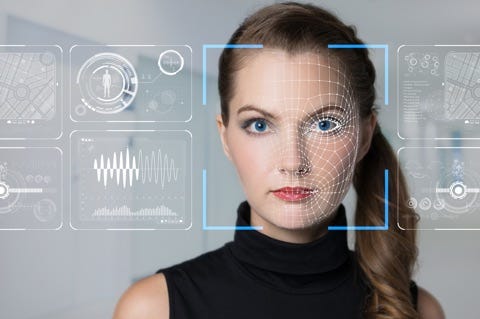
With the rise of credential stuffing and account takeovers keeping security professionals up at night, many pundits believe that biometric authentication is their answer.
But as any security veteran will tell you, there's never a simple solution. While biometrics do offer a stronger form of authentication than usernames and passwords, they come with their own risks. Several recent breaches and hacks by researchers exemplify the cracks that can show at the seams of any security model that relies too heavily on biometrics.
The permanence of physical biometric information can actually be a detriment to its use as an authenticator if attackers are able to compromise that data. Case in point is a breach that occurred several weeks ago, when security researchers found an unprotected and unencrypted database of biometrics identifiers run by the Biostar2 platform was putting millions of people's information at risk. The database included 23GB of data that included facial recognition information, unencrypted usernames and passwords, and the fingerprints of 1 million people.
One of the many shocking details of the devastating breach against the Office of Personnel Management (OPM) in 2015 was how attackers were able to make away with the fingerprints of 5.6 million federal workers. These prints were of some of the most sensitive government workers seeking security clearance from the government, making the repository quite valuable to the right adversary.
The trouble with the theft of fingerprints from repositories like Biostar and OPM is that attackers can fairly easily replicate them using everything from wax impressions to 3D prints modeled from stolen print info. The latter was demonstrated in April to work against Samsung's latest generation of fingerprint scanners on its Galaxy phones.
Earlier this summer, the US government reported that a third-party breach at a subcontractor for Customs and Border Patrol compromised a cache of facial recognition images. The breach put at risk nearly 100,000 images of travelers and license plates used by the agency for verifying and authenticating travelers' identities. The subcontractor, Perceptics LLC, had put the images on its IT servers, only to have them stolen in a malicious cyberattack.
Designed to offer better assurance than easily fooled fingerprint-reading technologies, palm-vein recognition isn't without its weaknesses, either. Last year researchers showed how they could create a fake hand out of wax and use it to game vein biometrics from Fujitsu and Hitachi. The process of creating the hand took about a month, using some 2,500 photos of vein patterns.
Earlier this year researchers with Kaspersky Labs discovered a lively market for stolen digital fingerprints. The cache of digital data shows that attackers are working hard to come up with bypasses around behavioral biometrics that create identity authenticators based on a cross-section of user behaviors and traits.
Many pundits say voice authentication is the answer to the hackability of other biometrics, like fingerprints. But the truth is that voice prints can also be gamed. Last year at Black Hat, researchers found that with about 10 minutes of sample audio from a speaker, they could crack numerous voice authentication systems. Considering that high-profile targets are likely to be on social media, conference websites, and other online arenas littered with public videos, it wouldn't be too hard for hackers to obtain their voice prints.
Many pundits say voice authentication is the answer to the hackability of other biometrics, like fingerprints. But the truth is that voice prints can also be gamed. Last year at Black Hat, researchers found that with about 10 minutes of sample audio from a speaker, they could crack numerous voice authentication systems. Considering that high-profile targets are likely to be on social media, conference websites, and other online arenas littered with public videos, it wouldn't be too hard for hackers to obtain their voice prints.
With the rise of credential stuffing and account takeovers keeping security professionals up at night, many pundits believe that biometric authentication is their answer.
But as any security veteran will tell you, there's never a simple solution. While biometrics do offer a stronger form of authentication than usernames and passwords, they come with their own risks. Several recent breaches and hacks by researchers exemplify the cracks that can show at the seams of any security model that relies too heavily on biometrics.
About the Author(s)
You May Also Like
CISO Perspectives: How to make AI an Accelerator, Not a Blocker
August 20, 2024Securing Your Cloud Assets
August 27, 2024




