Cyberspying Campaign Comes With Sabotage Option
New research from Symantec spots US and Western European energy interests in the bull's eye, but the campaign could encompass more than just utilities.
June 30, 2014
A well-heeled and aggressive cyber espionage operation out of Eastern Europe is targeting mainly US and other Western energy grid operators, electricity generation firms, and petroleum pipeline operators by planting Trojan-rigged software updates on the websites of the victims' industrial control system (ICS) software vendors.
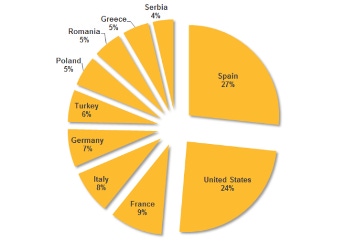
The attacks on energy industry vendors came to light last week when F-Secure revealed it had spotted the attacks targeting European energy firms. They are the handiwork of a nation-state backed hacking group called DragonFly, a.k.a. Energetic Bear, according to new research on the attacks published today by Symantec. Spain (27%) and the US (24%) were the nations with the most active infections via the attack campaign, followed by France (9%), Italy, Germany, Turkey, Poland, Romania, Greece, and Serbia.
Kevin Haley, director of Symantec Security Response, says the attackers are out of Eastern Europe and have in their arsenal malware that could be used to sabotage or disrupt the operations of their victims. "We have not seen any signs of sabotage." However, "the potential for that is clearly there."
Symantec spotted the group shifting more of its focus on to energy firms as of March, with half the targets in energy and 30% in energy control systems, followed by file hosting services and "unidentified" targets.
But Sean Sullivan, a security adviser at F-Secure, says the attacks -- which he confirms are out of Russia -- are not just about stealing information from or disrupting energy grid operators. "From what I've seen, it looks to me like they want a broad range of targets. The espionage going on here seems to be a wide net for any sort of infrastructure that might give the ability to get your way politically… That fits in with what I know of Russian tactics."
Commercial manufacturing operations are in the bull's eye, as well, he says, especially ones that supply the attackers' potential military adversaries.
[F-Secure has unearthed a new attack against industrial control systems that goes after European targets, using rare infection vectors. Read As Stuxnet Anniversary Approaches, New SCADA Attack Is Discovered.]
Neither F-Secure nor Symantec would name names, but at least three software vendors' websites were hacked, and their software update links were implanted with the so-called Havex or Oldrea backdoor Trojan, a custom remote access Trojan that fingerprints computers and other systems in a victim's network, including specific server information. ICS-CERT reports in its advisory on these attacks that the Havex malware can trigger intermittent denial-of-service attacks on ICS applications.
According to Symantec, some victim organizations downloaded the malware when updating their ICS software, giving the attackers a foothold into their networks as well as a means to sabotage their operations on those systems. Havex/Oldrea gathers system information, lists of files and programs on the infected machine, and available drives, as well as Outlook address book and VPN configuration information.
Most of the command and control servers are hosted on hijacked content management systems, and the attackers also sometimes employ the Karagany Trojan, which is available in the cybercrime underground market. "Karagany is capable of uploading stolen data, downloading new files, and running executable files on an infected computer," Symantec said in a blog post today. "It is also capable of running additional plugins, such as tools for collecting passwords, taking screenshots, and cataloging documents on infected computers."
The DragonFly/Energetic Bear gang has been in action at least since 2011 and originally focused its efforts on US and Canadian defense and aviation companies, according to Symantec. The traditional approach to attack was spearphishing and later watering hole attacks where it infected websites its targets would most likely visit. Targeting their software vendors was yet another attack vector.
This isn't the first time attackers have used their targets' software vendors as a vector of infection. "We've seen the Hidden Lynx group do similar" things, Haley said. Hidden Lynx was behind the attack on Bit9; attackers stole one of the security vendor's digital code-signing certificates and used it to sign malware in attacks against some of its customers.
"The attackers are collecting logins, passwords… we saw them stealing from Outlook," as well, Haley said.
F-Secure's Sullivan said his team has witnessed several connections to the attackers' command and control servers from Tor anonymized nodes. They also saw the attackers using the "Fing" application, which scans and takes inventory of a network. "We think the folks behind this are collecting as much as possible… and seeing what might be useful in soft power deployment."
He worries that the conclusions have been pointing too quickly to an energy sector attack only. "This is a very broad-based" campaign to cripple adversaries, including via manufacturers that supply their armies with food and other crucial items.
About the Author(s)
You May Also Like
Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024Finding Your Way on the Path to Zero Trust
May 22, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


