Why Threat Intelligence Is Like Teenage Sex
Everyone thinks everyone else is doing it, and most of the few people who are actually doing it aren't doing it all that well.
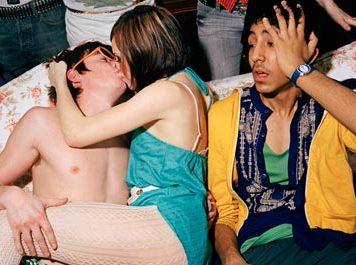
Whatever the official theme of the 2014 RSA Conference was, any one attendee will tell you the unofficial theme -- the message on every banner in the place, it seemed -- was “Threat Intelligence.” But threat intelligence, as it was put to me by Eric Olson of Cyveillance, is a lot like teenage sex: Everyone is talking about it, everyone thinks everyone else is doing it, and most of the few people who are actually doing it aren't doing it all that well.
There are lots of fashionable things to say about intelligence, and everyone gets all… cool when they discuss it, as if they have some dark, national secret that you don't have. Balderdash!
Let's cut through the mystery in two important ways:
Threat Intelligence is not nation-state espionage. You're bringing data together, and adding value to it by delivering usable information to those who need it. Put your cloak away.
You're not looking to solve Mideast peace. You're looking to empower your decision makers to make your organization more secure. Keeping it simple helps drive success.
My observation from several circuits through the RSA Conference exhibition floor is that there is a classic conflation among data, information, and intelligence. You can find many definitions of “intelligence” out there, but I'll just go out on a limb and say that, without analysis, a nugget from a “threat feed” (in which you might learn that IP address 1.2.3.4 is “known-bad”) is not intelligence. It is a datum.
Even the database itself is not intelligence, per se. It turns out that a database is just a collection of data. Don't get me wrong: The data within the database -- or the threat feed -- can be highly useful to the intelligence process. But (and I am not picking nits here) it comprises a data feed, not an intelligence feed (except to marketers).
Simply, albeit admittedly incompletely, put, intelligence is analyzed data that you can do something useful with.
For example, the fact that a given IP address has been observed to be associated with some given nastiness does not mean that the nastiness applies to you in the same way it applied to the earlier observer, or even that it applies to you at all. Analysis of the data in context of your mission, goals, and tactics is required before this datum rises to the level of employable intelligence.
The fact that something is in a threat database does mean, though, that someone has analyzed it and determined it is useful in the context of a threat database. But expecting that you can buy access to a feed of pre-packaged data that is sold to thousands and that it will be pre-analyzed within your use context is like buying a guitar and expecting that it's been tuned at the factory.
Rule of thumb: Intelligence is not something you can buy in a feed -- even if it comes from Mandiant.
Now that internal intelligence programs are becoming the “must have” thing in enterprise, here are two observations:
First, hooray! Threat intelligence has left the bleeding edge and is becoming an early mainstream capability. If you care about information security, a robust threat intelligence program is an essential enterprise capacity.
Second, before you meet with a single vendor selling “threat intelligence,” it's equally important that you understand what you want your threat intelligence to actually do inside your organization, and how you will leverage it to accomplish those goals.
Data synthesis (or, if you're a real dag, "dot connecting") only works when an effort to bring data together meets executive desire, cross-stovepipe authority, and application of technical and analytical resources.
Perhaps most important, a successful enterprise intelligence operation must be a defined, funded strategic undertaking of the organization. This doesn’t mean it must be expensive, merely that it must be defined and agreed upon. Set the bar low at first, then build on success.
So, the real question isn't “Which threat feed to I buy?” but rather it's “What do you want your intelligence to allow you to do?” The answer informs the data acquisition strategy. For example, are you staying ahead of fraud by keeping up to date with tactics? Tracking legislation? Trying to get a jump on malware that could hit your systems?
Any of these is a reasonable goal, but you need to decide on your goals.
Think strategically about what you want, then articulate the strategy clearly. And provide the resources to develop the tactical.
Give someone responsibility for and authority to run an intel shop. Get someone who’s done it before to be that someone. They don't have to be a retired general. They need to have experience, and be able to articulate the vision to the executives and the specifics to those in the trenches.
As Clint Bruce likes to say, the person who runs your intelligence operations should have the capacity to "Love the men, explain the mission, and don't be a detriment to the fighting."
Then leverage, leverage, leverage.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




