Wolfe's Den: Airport Scanner Patents Promise Not To Show Your 'Junk'
Rapiscan, the company supplying the controversial x-ray backscatter screeners, has won a patent for a machine which detects threats "with minimum display of anatomical details." Its competitors, and body scanner pioneer Martin Annis, are also pursuing enhanced privacy approaches. Here are the technology details.

5 Airport Body Scanner Patents Stripped Down
(click image for larger view)
Slideshow: 5 Airport Body Scanner Patents Stripped Down
Are the airport body scanners, which have provoked a raging controversy, "porn machines," as they've been dubbed by Atlantic blogger Jeffrey Goldberg? Or are they the most effective means going of identifying terrorists carrying explosives?
A bunch of U.S. patents I've dug up indicates that the former is definitely not the manufacturers' intent, notwithstanding the 100 leaked naked body scans posted recently by Gizmodo. Those scans, btw, were at a courthouse, not an airport. They're very blurry besides, though this picture from one of the Rapiscan scanners actually used at U.S. airports is anything but.
As for the effectiveness of backscatter X-ray technology at sussing out bombs, that's an issue open to debate. Experts have pointed out that the machines will not reveal contraband secreted in a bodily orifice (nor, it is to be hoped, will the TSA pat downs). Other observers have noted that the long airport lines snaking toward the security checkpoints are themselves unprotected targets, which are scarily ripe for suicidal terrorists.
Finally, health activists have raised alarms about yet another source zapping people with X-rays. For its part, Rapiscan claims that exposure levels are so low, an individual can safely undergo "up to 5000 scans per year." (If so, maybe they should install the machines at the Admirals Club.)
Me, I stumbled thru a non-opt-out scan on Nov. 18 at SFO. At the time, I hadn't been aware of the debate, which was shortly to go viral. So I wondered what the heck was up with the machine to which I was being directed. At first glance, it reminded me of a revolving darkroom door, but also could've been a salvaged "Orgasmatron" from Woody' Allen's 1973 film "Sleeper."
The experience itself was uneventful, though I have to say I wasn't happy with the "Up Against The Wall" position one is directed to assume while being imaged. On a technical basis, it did occur to me that, if these machines can photograph genitalia, they should also be able to visualize feet, in which case can't we all just put our shoes back on?
Mostly, my reporter's eye was curious about the technology behind the airport body scanners, which I suspected was being mis-, or at least loosely, characterized by writers who hadn't bothered to do much digging. (In their collective defense, what Web worker has time for that nowadays?)
So I went where I always go, to the patent record, and dug up some interesting information.
As a quick intro, before we dive into five patents I've selected, here are a couple of stories worth check out. This AllBusiness article gives a quick overview of the airport scanner marketplace. Three companies were originally competing to win the U.S. airport body scanner contract: Rapiscan Systems Inc. , of Torrance, Calif., L-3 Communications Security and Detection Systems Inc., of Woburn, Mass., and American Science and Engineering Inc. (ASAE) of Billerica, Mass.
Rapiscan won the contract as the sole supplier of airport scanners in Sept. 2009. (Rapiscan's representation by former DHS Secretary Michael Chertoff has been much in the news recently. )
ASAE is notable because it was found by Martin Annis, who was recently identified in this New York Times article as the father of X-ray body scanners. Annis is no longer associated with ASAE, but even in his mid-80s he is still cranking out scanner patents, as we shall see shortly.
5 Airport Body Scanner Patents Stripped Down
(click image for larger view)
Slideshow: 5 Airport Body Scanner Patents Stripped Down
The Patents
I've selected five recent scanner patents, not randomly, but because they all illustrate salient points about the technology. Go to the companion slideshow to see relevant diagrams from each the patents.
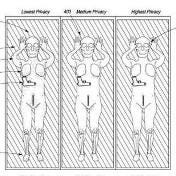
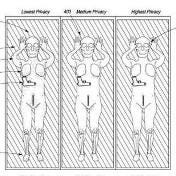
The first patent, number 7,796,733, is entitled "Personnel security screening system with enhanced privacy." It was awarded this September to inventor Ron Hughes and Rapiscan. (Technically speaking, it was assigned to PatentMatrix, which is some kind of patent intellectual property management house, but it's a Rapiscan patent.)
This patent is interesting because it clearly shows that scanner manufacturers are aware of privacy concerns. Thus, the fault with leaked images probably lies more with process and usage scenarios than it does with the machines themselves.
The technical challenge in obscuring the naughty bits is that it also tends to null out what you're looking for. Or, as the Rapiscan patent explains it: "Conventional image processing techniques for protecting privacy, tend to diminish non-body images as well."
The application continues: "What is needed therefore is an image processing technique that allows for maximum threat detection performance with minimum display of anatomical details." That's accomplished using a composite imaging technique. The result is a system which "does not require the operator to view an actual image of the subject's body to obtain an indication of potential objects desired to be detected."
That's good news. OTOH, one can wonder whether or not there's a smokescreen element to the privacy stuff. As in, are real-world operators going to see the mannequin-like images promised by this patent, or full frontals like this CNET grab?
Rapiscan's November Patent
A more recent Rapiscan patent, number 7,826,589, is interesting because it shows the continuing evolution of the company's technology. This patent is entitled "Security system for screening people." It was awarded on Nov. 2 to inventors Andreas Kotowski and Ron Hughes.
It's billed as "an X-ray screening system capable of rapidly screening people for detection of metals, low Z materials (plastics, ceramics and illicit drugs) and other contraband which might be concealed beneath the person's clothing or on the person's body."
This patent carries forward the privacy shield of the previous invention, "provid[ing] a means for creating a non-human representation of the body being examined to thereby permit faster inspection with less invasion of privacy."
Pioneer's Patent
Now we're on to two patents by body scanner pioneer Martin Annis. The Times article pointed out that Annis's first scanner patent came in 1980, so he gets points for persistence.
In patent 7,561,666, awarded in July, 2009 for a "Personnel x-ray inspection system ," Annis also appears to address the health concerns raised by the scanners. "An object of the present invention is to provide a personnel inspection system that detects contraband better than systems of the prior art while using less power," says the patent.
5 Airport Body Scanner Patents Stripped Down
(click image for larger view)
Slideshow: 5 Airport Body Scanner Patents Stripped Down
It's also got a highly sophisticated X-ray setup. Beams of higher and lower x-ray energies are chopped into a fan pattern by a rotating disk, the better to "enable differentiation between innocent and contraband materials."
In his second patent, Annis is reshuffling the scanner deck by from airport applications to medicine. Patent 7,620,150, of Nov. 2009, is entitled "X-ray backscatter system for imaging at shallow depths ."
From the description: "The invention relates to medical diagnostic systems, more particularly, to diagnostic instruments for detection of tumors of the skin."
The idea is to do it at lower power and with greater detail than conventional systems. More from the patent: "Current x-ray procedures for examining the region of the body just below the surface of the body utilize transmission x-ray systems. These systems must penetrate the entire width of the body that lies below the region of interest just below the skin lesion. In order to do this, the peak energy of the x-ray spectrum must be sufficiently high to penetrate the body and the x-ray exposure to the patient is correspondingly high. In addition, the contrast in observing small differences in the density in the soft tissue is not sufficiently great to make such an x-ray examination useful.
"It is important that the system be of low radiation exposure to the healthy tissue deep within the body. This is accomplished in the current invention by using backscattered x-rays that expose only a relatively small volume of the patient's body. The system is also compact and inexpensive, which is desirable given the large number of patients that must be served in doctor's offices."
A specific application noted by Annis is to check out suspicious regions of the breast, which have initially been identified during mammography.
L-3's Patent Application
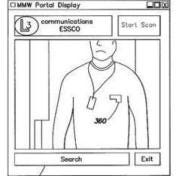
Our fifth and final example is from L-3 Communications. The company didn't win the airport contract, but it is still very much a player in explosive detection, selling systems to the military. What we're looking at here is not an awarded patent, but rather patent application number 20100141502, which was filed this past June.
The application is entitled, "Contraband Screening System With Enhanced Privacy." The documentation shows that L-3 is pursuing the techniques for muting out raw-body images to focus instead on the bad stuff.
Here's the money quote: "The system preferably does not directly display images of a person formed from a mm wave camera scan. Doing so creates privacy concerns. Because the millimeter (mm) wave camera effectively "sees through" clothes, an image formed with the mm wave camera resembles a picture of a person taken without clothes. Thus, detecting contraband in a mm wave image but displaying an indication of the contraband in connection with a visible light image addresses potential privacy concerns as well as presenting the information in a format readily understandable to the human operator of the inspection system."
FOR FURTHER READING
Wolfe's Den: IBM Patenting Airport Security Profiling Technology
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




