Americans Ignoring Social Media Privacy Risks
Users are worried about the dangers of disclosing personal information on Facebook and other sites, but they do it anyway, finds Lawyers.com study.


Best Mobile Apps For Busy Professionals
(click image for larger view)
Best Mobile Apps For Busy Professionals
Despite realizing the dangers of posting personal information on social networking sites, Americans continue to divulge a lot of data about themselves, a new study by Lawyers.com found.
Half of American social media users surveyed admit to seeing people disclose too much personal information online, yet 28% of social media users admit to rarely considering what could occur if they share too much private data online, the report said.
About 44% of those surveyed are concerned that the personal information they share on these sites is being used against them, while 21% of Americans who use social media sites believe people who take advantage of weak privacy settings on these sites already have accessed their personal information, according to the poll.
The study was released about a week after 10 of the most popular Facebook apps were found sharing members' user ID numbers with outside companies, and three of the top 10 Facebook apps, including Farmville, shared information about users' friends. Lawyers.com, which is designed for consumers and small businesses, is operated by LexisNexis Martindale-Hubbell, which commissioned TNS Global to conduct the 2010 Lawyers.com Social Networking Survey of 1,000 adult Americans.
"The Lawyers.com Social Networking Survey reveals a clear disconnect between the privacy concerns of users and their actual behaviors and disclosures on social networking sites," said Carol Eversen, VP of marketing at LexisNexis. "Nearly every week we hear about the negative consequences resulting from inappropriate disclosures and uses of personal information on social networking sites, however the data suggests that Americans are not taking the necessary steps to protect themselves."
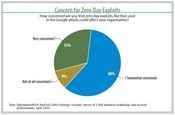
Strategic Security Survey: Global Threat, Local Pain
Strategic Security Survey: Global Threat, Local Pain (click image for larger view and for full slideshow)
Of those using social media sites, 69% of respondents admit to posting their first and last names, 67% have posted their photograph, and 51% have included an email address. In addition, 16% have shared travel plans, 7% have posted their cell phone number, and 4% have revealed their home address, the study found.
It is difficult for many to decide how much is enough, according to the report, which found that 46% of Americans agreed that sometimes it is hard to determine what information to share and what to keep private.
One-quarter of poll respondents have seen social network members misrepresent themselves, through steps such as posting false information or creating fake profiles. And 14% said strangers communicated with them because of information they shared on a social network.
There are other downfalls to sharing too much information online. For example, 11% cited someone posting unflattering photos; 7% said a personal relationship with family or friends was affected because of revealing too much information; and 6% were concerned about being reprimanded because of something they posted. But 38% of those queried agreed with the statement that those who share too much online deserve to have that information used inappropriately.
However, social media sites do not escape blame: 76% of Americans were concerned that social networking sites are inadequately protecting users' personal information, the study found. And 43% admitted they typically hit "agree," without reading the site's terms and conditions, according to the report.
When it comes to work and the web, Americans are mixed, with 40% believing managers have the right to monitor their employees' personal tweets and Facebook pages, with an equal number of Americans believing they could lose their jobs because of information they've posted on social media sites. But 53% of respondents said inappropriate remarks on social media sites should not impact employment, the study found.
About the Author(s)
You May Also Like
Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024Finding Your Way on the Path to Zero Trust
May 22, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024