CopyCat Malware Infects 14 Million Android Devices
A new malware strain is discovered with a novel approach to infecting Android handheld devices with adware.

Millions of Android devices have been hit with a new malware strain called CopyCat that uses a unique approach to injecting the devices with adware, according to a researcher with Check Point's mobile research team, which released its findings today in a blog post.
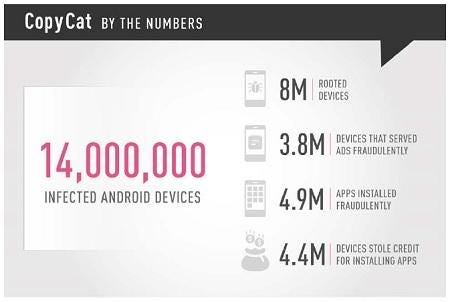
CopyCat's malware infected 14 million Android devices, with the majority hitting Asia (55%), followed by Africa (18%), and then the Americas (12%).
Check Point first ran across CopyCat in March, after one of its enterprise customers was attacked by the malware. However, the security company believes the CopyCat campaign hit its peak between April and May of 2016.
"While other adware [has existed] for a long time now, we can't really identify CopyCat with any known malware family, and it introduced new tactics which were never seen before," says Daniel Padon, a Check Point researcher, who noted it does not behave like other known adware families like HummingBad and Gooligan.
CopyCat is believed to have spread by phishing scams and repackaging popular apps with malware as users download them from third-party app stores, according to Check Point.
After infecting the Android device, it roots the device to take full control of it. The malware then injects the Zygote launching process app with code to begin installing unauthorized apps onto the device.
Adware Twist
What is novel about CopyCat is what happens once it detects that an unauthorized app has been installed.
"The really interesting technology it uses to steal revenue is taking credit for advertising ads that led to installations of apps. It simply switches the real referrer's ID with its own once it detects an installation process," Padon explains.
By using a separate module to install the fraudulent apps and swapping out the referrer's ID, the cyberthieves get the credit – and the revenue – for having installed the app and displaying the fraudulent ads.
Check Point estimates the attackers who created CopyCat have generated $1.5 million in revenue. Check Point found CopyCat may have possible ties to MobiSummer, a Chinese ad network, but it is hard to determine if this group is involved with CopyCat intentionally, says Padon.
 [Source: Check Point]
[Source: Check Point]
Versions of Android 5 or earlier are vulnerable to rooting exploits, says Padon. He notes that Google estimates 60% of its mobile users are on Android 5 or earlier versions.
In addition to CopyCat, another Android malware strain that roots devices was recently discovered. Palo Alto Networks today noted it discovered SpyDealer, which gains root privilege using Baidu Easy Root and then steals sensitive data from more than 40 apps that may be loaded on the device. This malware affects Android devices with versions 2.2 to 4.4, which accounts fpr approximately 25% of Androids worldwide, according to Palo Alto Networks.
After Check Point made its discovery in March, it notified Google. And although the malware appears not to be coming from apps in the official Google Play store, Google was able to mitigate the CopyCat campaign, Check Point notes in its blog.
Although patches exist for all vulnerabilities used by CopyCat, Padon notes Android devices suffer from a severe lack of patching. That, in turn, makes it easier for attackers to install CopyCat.
 Black Hat USA returns to the fabulous Mandalay Bay in Las Vegas, Nevada, July 22-27, 2017. Click for information on the conference schedule and to register.
Black Hat USA returns to the fabulous Mandalay Bay in Las Vegas, Nevada, July 22-27, 2017. Click for information on the conference schedule and to register.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




