Infographic: Mobile Security Run Amok
Where is your organization in the battle over mobile device management and security?
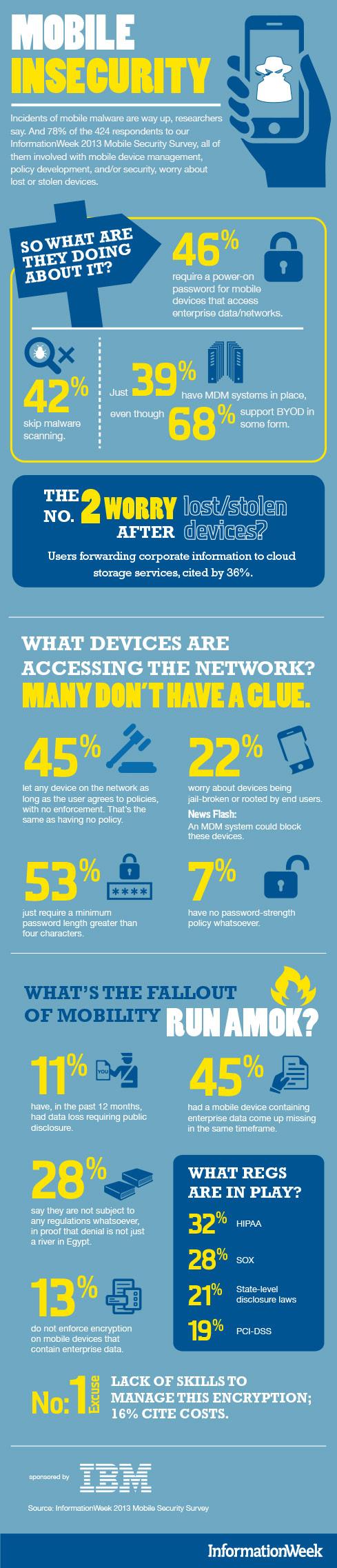
2014 marks the 10th anniversary of the world's first mobile malware, Cabir. In the decade since, the incidents of mobile malware have increased dramatically. Yet, according to InformationWeek's 2013 enterprise security survey, the majority of security pros still don't have a clue about what devices are accessing their networks.
Where is your organization in the battle over mobile device management and security? Check out the graphical depiction of the research below, then let's chat in the comments about the challenges you face.
About the Author(s)
You May Also Like
Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024Why Effective Asset Management is Critical to Enterprise Cybersecurity
May 21, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




