
Cybersecurity In-Depth: Feature articles on security strategy, latest trends, and people to know.
The Center for Long Term Cybersecurity recently awarded grants to six artists in a contest to come up with ideas for works with security themes and elements. Check 'em out.
October 10, 2019


Image: kirasolly, via Adobe Stock)
Powerful art can cause upset as easily as it can soothe. At its most effective and high functioning, art fosters conversation and changes the ways we think about challenging topics — like cybersecurity.
That, in a nutshell, is the driving force behind a series of grants the Center for Long Term Cybersecurity (CLTC) recently awarded to six artists in a contest to come up with ideas for works with security themes and elements.
"Cybersecurity works like an emergency room, where you fix it up and send it back out," observes Ann Cleaveland, executive director of CLTC, part of UC Berkeley. "We want the world to take a longer-term view." The winning artists' proposals are intended to invite viewers into that perspective, she adds.
Projects were considered for their potential to illuminate the human impacts of security and provoke critical dialogue about important issues, such as privacy, surveillance, cyberattacks, and malware, according to the center. Winning artists will receive anywhere from $5,000 to $25,000, and CLTC will help the artists show and publicize their works, which will debut sometime in 2020.
The Cybersecurity Arts Contest was launched as part of the Daylight Security Research Lab, a new initiative and offshoot of CLTC that aims to shift how people identify and understand technology's potential ills. "The imagery we have — the hacker and the hoodie, or green screens of code streaming by — doesn't really resonate with security professionals," says Nick Merrill, director of the lab.
And outside the world of security, the images don't foster understanding or insight. "Our biggest hope is that the artists will create works that change the way people think about security — and how decision-makers approach it," Merrill adds.
Contest entries showed tremendous creativity and will challenge norms and assumptions about security, Merrill adds. "It's an experiment … no one's done anything like this, so we don't know what will come of it," he says.
Browse on for the six winning projects.
Figure 2:
'between systems and selves,' by Caroline Sinders
Malware as a source of creative inspiration and artistic choices? Artist Caroline Sinders will use Mirai and other malicious code to help determine shapes and colors of a series of "poetic sculptures" she'll create with her CLTC grant.
Sinders' project will analyze various malware against a series of parameters that then get translated into structures that will make up the sculpture, which could exist as mobiles that hang from a ceiling, for example. She imagines between 100 and 1,000 small sculptures made out of either metal or thin wood.
"So much of code plays with literal human words but uses technical processes that are hard to describe," Sinders explains. "An algorithm can do things, but why it does things is based in the math that is within the algorithm. Malware is a kind of technical algorithm in what it does." Sinders will thus attempt to make malware and algorithms "human readable" in the resulting sculptures.
Sinders wants viewers to see that technical systems can be rendered in beautiful, minimal ways. "Technical complexity doesn't always mean aesthetic complexity," she says. And since security and privacy affect everyone, "art can help translate and make certain fields or ideas feel more applicable and real to a general audience," Sinders adds. "Art can add poetry to space that has felt cold, mechanical, distant or confusing."
In other words, a perfect addition for every data center and SOC out there.
(Image: Caroline Sinders)
Figure 3: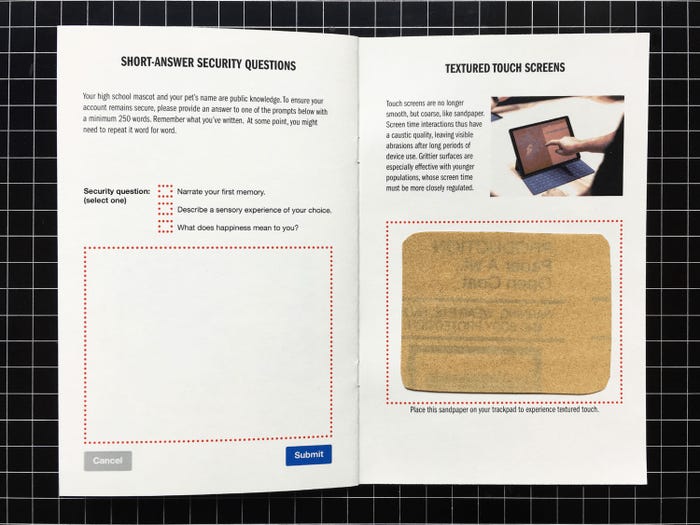
'Hack Back,' by Joyce Lee
With clapping back an official thing on social media, Oakland, Calif.-based "design researcher" Joyce Lee has tentatively titled her grant-winning "zine" publication "Hack Back," with a focus on the human aspects of cybersecurity. The zine is intended to educate and foster security awareness, including "accessible instructions for risk mitigation." (At last!)
Lee will use "Hack Back" to focus on cryptography, passwords, account management, and social engineering attacks with content that is "both playful and practical, activating cybersecurity awareness by directly engaging readers in provocative exercises," the CLTC grant winner says.
"Hack Back" will be published in a paper workbook format. Lee says the medium may not seem like the best choice to discuss digital security, but that paper's "antithetical nature is surprisingly appropriate for imagining alternative realities as well as reshaping security-related decision-making and behaviors," she wrote in her proposal. Lee pointed to paper publications such as "The Whole Earth Catalog," which in her view helped to shape early tech culture.
Lee will use her funding to bring the security-themed zine to Oakland, San Francisco, Los Angeles, Portland, Chicago, Toronto, and New York. She will distribute "Hack Back" at DIY events, workshops, libraries, bookstores, and other outlets. By leveraging public events, Lee seeks to empower those concerned with the effects of surveillance and ubiquitous computing but who may lack the technical literacy to identify threats and fashion a defense. Lee's zine format may be just the ticket for improved security for the masses.
(Image: CLTC)
Figure 4:
'The Price is Wrong,' by Shayna Robinson & Neema Iyer
This three-part "mockumentary" will track the stories of various participants and examine their digital hygiene as they answer questions while riding in an Uber in Kampala, Uganda. The idea is the brainchild of Shayna Robinson and Neema Iyer, both of whom work for the digital think tank Pollicy.
Pollicy describes itself as a group of technologists, data scientists, creatives, and academics looking to innovate government service delivery in Africa. "We work with governments, civil society, NGOs, and the private sector re-design services around citizen needs and demands," according to the organization's website. "We believe in co-designing and co-creating better experiences." Pollicy employs all manner of strategic consulting, user-centered design, research, and capacity development with governance players to achieve that.
Robinson and Iyer view "The Price is Wrong" as an entry point to discuss cybersecurity in the African context through a lens of comedy and realism. Working in a style similar to "Cash Cab," each 10-minute episode teases out online behaviors of participants, ultimately testing how much value they place on their personal data and security, according to Robinson, Pollicy's head of R&D, and Iyer, the organization's founder and director.
(Image: CLTC)
Figure 5:
'SweetWire,' by Greg Niemeyer
In pitching the CLTC on the concept of "SweetWire," "data artist" Greg Niemeyer hopes to create a music video that takes the successful containment of a cybersecurity attack and turns it into music and choreographed movement.
Switzerland native Niemeyer was named a professor for new media in art practice at UC Berkeley in 2001. He co-founded and directed the Center for New Media, focusing on the critical analysis of the impact of new media on human experiences. His work includes collaborations across disciplines and across media, from gravure etchings to virtual reality, "with an eye for the poetic foundations of technical protocols," according to his website.
Structurally, Niemeyer envisions the "SweetWire" music video as a dialog between a hacker and the hacker's target. This approach casts cybersecurity as an ongoing dialog arising from the need -- and inherent tension -- to balance security and connectivity, and as an ongoing effort to distinguish legitimate transactions from illicit ones. The music will be produced by Niemeyer in collaboration with Ph.D. students in music at UC Berkeley, as well as with Oakland-based music producers from Youth Radio. It's a curious collaboration and a bridge between the hard edges of technology and the poetry of dance and music.
(Image: Greg Niemeyer)
Figure 6:![]()
'Tally,' by Joelle Dietrick & Owen Mundy
A technology challenge like security deserves a technology-based project as part of the CLTC mix. A software-based blob called Tally fills the bill here for the creative team of Joelle Dietrick and Owen Mundy, who are also real-life spouses.
Dietrick's paintings, drawings, and animations "explore contemporary nesting instincts and their manipulation by global economic systems," according to her website. And Mundy is an artist, designer, and programmer whose research investigates public space, information privacy, and big data.
In their joint proposal, they posit that Internet users are frequently unaware of how they continually expose private information about themselves through cookies and other digital trackers as they browse, post, and consume Web content. Dietrick and Mundy aim to shake that up through their creation, Tally, "a free, open-source browser extension that transforms the data that advertisers collect into a multiplayer game," they explain.
Once installed, Tally appears on the corner of your screen as a friendly pink blob who also warns you when companies translate your online experiences into free behavioral data. That's a good friend to have in this day and age of free social media, free webmail, and other allegedly free services.
(Image: Joelle Dietrick)
Figure 7:
'Virtual Caring,' by Lauren McCarthy & David Leonard
As voice recognition and artificial intelligence enter the consumer technology mainstream, it's only natural that users are turning to Alexa and Google Home to help out with caring for elderly relatives. In the CLTC project "Virtual Caring," Los Angeles-based artists Lauren McCarthy and David Leonard will explore the links among elder care, AI, and surveillance.
McCarthy's previous works have examined social relationships in the midst of surveillance, automation, and algorithmic living. She's also the creator of p5.js, an open-source programming language with over 1.5 million users, for learning creative expression through code online. Leonard works in video and the visual arts.
The two creators plan to install a network of remote-controlled cameras, microphones, lights, locks, and appliances in the homes of elderly subjects. Their plan is to then serve as virtual caregivers, responding to the residents' requests — and even proactively making suggestions — while documenting the undertaking with a series of 360-degree cameras, according to McCarthy and Leonard. With so much focus on aging in place among Baby Boomers, the project could yield useful insights – and places where technology is indeed intrusive.
(Image: Lauren McCarthy)
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024

