Security updates patch bugs being exploited via in-the-wild attacks, except for Windows XP, which now becomes a sitting duck.

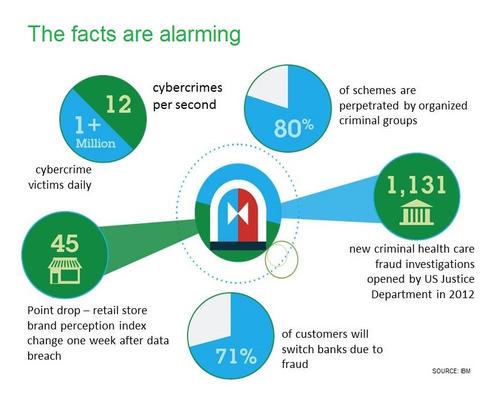
10 Ways To Fight Digital Theft & Fraud
10 Ways To Fight Digital Theft & Fraud (Click image for larger view and slideshow.)
Microsoft has released a slew of security updates, including fixing two sets of vulnerabilities that are being actively exploited by in-the-wild attacks. But for the first time ever, Windows XP holdouts didn't receive any related security updates.
Microsoft published eight security bulletins Tuesday -- as part of its regularly scheduled monthly patch release cycle -- including fixes for 13 different vulnerabilities in Windows, Internet Explorer, Office, SharePoint Server, Group Policy preferences, as well as the .NET Framework and iSCSI.
Microsoft's cumulative IE security update includes a fix for an "out-of-band" patch that it originally released May 1, to patch a critical IE bug (CVE-2014-1776) that Google's security team found was being actively exploited by attackers to remotely execute arbitrary code. In a surprise twist, Microsoft had released the patch for Windows XP, which it officially stopped supporting last month.
Microsoft also issued a fix for a new critical IE bug Tuesday, saying that it was aware of limited, targeted attacks that attempt to exploit this vulnerability.
[Should government investigators be given expanded powers to battle cybercriminals? Read FBI Seeks License To Hack Bot-Invested PCs.]
Wolfgang Kandek, CTO of Qualys, described the patch in a blog post as "another surgical fix" similar to the May 1 patch. He noted that anyone who has yet to install the May 1 patch -- aside from XP users -- can install Microsoft's May 13 update instead, because it includes the fix.
Microsoft said that most customers have automatic updating enabled and will not need to take any action because this security update will be downloaded and installed automatically.
According to Dustin C. Childs, group manager for incident response communications at Microsoft's Trustworthy Computing Group, the IE update should top the list of enterprise patching priorities, followed by installing fixes a vulnerability in the MSCOMCTL common controls library included in Office -- which Microsoft said is also being actively exploited by in-the-wild attacks -- and a Group Policy preferences flaw.
Kandek concurred with that patch prioritization assessment, noting that the MSCOMCTL fix comes in the form of a new DLL that has ASLR set, an easy fix for the developers to implement (basically a recompile), but one that took extensive testing as this DLL is widely used. Thanks to ASLR -- address space layout randomization -- the update will also better block future attacks. Meanwhile, Kandek added, the Group Policy patch prevents the storage of credentials in Group Policies, where they are relatively easily accessed by hackers and pen testers alike.
CrowdStrike CTO Dmitri Alperovitch, via Twitter, lauded the latter fix. "Very good security update from Microsoft today that disables a number of password dumping tools including Mimikatz," he said.
Rounding up other security updates, any business that uses SharePoint should also prioritize a related patch from Microsoft, Kandek advised, especially if you expose SharePoint to the Internet. That's because the patch fixes a flaw that would allow a remote attacker to upload files to SharePoint and trigger remote-code execution, thus allowing the attacker to take control of the server.
"The silver lining is that this is what's known as an authenticated vulnerability,
so only users who have already logged in to your SharePoint server can mount an attack," said Paul Ducklin, head of technology at Sophos, in a blog post.
Adobe patches critical Reader, Acrobat, Flash flaws
Also on Tuesday, Adobe released patches for 18 flaws in its products. The security fixes affect Adobe Reader and Acrobat, Flash Player, Adobe Illustrator (CS6), and Adobe AIR running on Windows and Mac OS X systems, as well as the Linux version of its Flash Player. Adobe also updated its Flash Player plug-in for the IE10, IE11, and Google Chrome browsers to fix security problems.
All of the flaws, except the Illustrator update, have been rated at maximum severity, because they could be exploited by attackers to remotely compromise Windows, Mac, or Linux systems.
Adobe's IE plug-in updates also led Microsoft to revise a security warning it first issued in September 2012, detailing how attackers could create malicious websites to exploit a particular Flash Player flaw via drive-by attacks. Microsoft said that anyone who uses Flash Player must update, regardless of which browser they regularly use, since attackers could still trigger the IE flaws. "Other applications, such as Microsoft Office 2007 and Microsoft Office 2010, can invoke Adobe Flash Player in Internet Explorer," the company warned.
Accordingly, Microsoft urged anyone using Flash Player for IE10 (on Windows 8, Windows Server 2012, or Windows RT) or IE11 (for Windows 8.1, Windows Server 2012 R2 or Windows RT 8.1) to update their Adobe plug-in immediately.
Windows XP users now vulnerable
May is the final month that Adobe will release patches that work with Windows XP. Meanwhile, although Microsoft released an emergency IE fix May 1 that works with XP, Tuesday's batch of patches don't work with the XP, thus making it official that the operating system is no longer supported.
"Windows XP will not be receiving any security updates today," said Microsoft's Childs Tuesday in a blog post. "For some time we have been recommending customers move to a modern operating system like Windows 7 or Windows 8.1 to help stay safe, and now is a great time to make that move."
Microsoft, of course, has been sounding that drum for some time, and many businesses have adopted more modern versions of Windows. "Fortunately, the XP user base continues to shrink," Qualys CTO Kandek said, noting that the XP enterprise install base appears to have dropped to about 8%.
Figure 1: 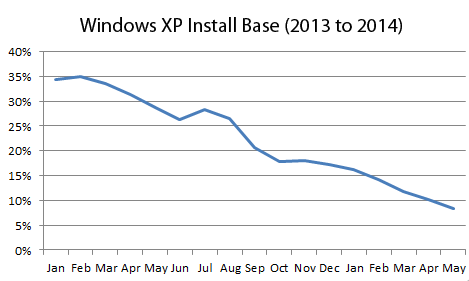
That's good, because from an information security standpoint, Windows XP users are sitting ducks, owing to hackers now being able to reverse-engineer flaws patched by Microsoft, then target those bugs in unpatchable XP systems. "The majority of the vulnerabilities addressed in the [Tuesday] updates probably affect Windows XP/Office 2003 ... but only users who have Microsoft's extended support agreement can get the patches," said Kandek.
Attackers' job will be made easier by Microsoft continuing to patch Windows Server 2003, which shares a substantial amount of code with XP. Accordingly, Kandek said, "We can assume that any vulnerability ... for Windows Server 2003 is applicable to XP as well." For this month alone, that means six newly patched flaws -- including the IE patch, ASLR fix, Group Profile patch, and Office updates, as well as the Adobe Reader and Flash fixes -- could be used by attackers to target XP systems.
Cyber-criminals wielding APTs have plenty of innovative techniques to evade network and endpoint defenses. It's scary stuff, and ignorance is definitely not bliss. How to fight back? Think security that's distributed, stratified, and adaptive. Read our Advanced Attacks Demand New Defenses report today. (Free registration required.)
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




