Deploying focused edge protection on-site extends security beyond the network level to shield millions of previously exposed devices, apps, and control systems.
The need for security is not new. We've seen devastating cyberattacks across every industry and type of organization, from the breach of millions of consumer logins to state-sponsored cyberwarfare against the military. But these events don't occur because of a blatant lack of security; actually, most organizations do have some form of cybersecurity.
While one in four organizations have designated cybersecurity teams, still 40% of all US businesses encountered at least one ransomware attack last year. The numbers continue to worsen as businesses begin to interconnect their systems — often a mix of legacy and modern Internet of Things (IoT) — and create webs of smart machines that can spread information, and malware, at lightning speeds.
The outlook is grimmer for industrial operations, which are controlling some of our most critical infrastructure and assets, and undergoing rapid modernization. Deloitte found that in 2016, companies in the energy sector reported 20% of all cyber incidents, coming in third behind manufacturing plants and communications networks. As these industries become increasingly "smart" and connected, the security risks multiply.
Historically, industrial operators "air-gapped" their networks, restricting access to their control devices and systems by isolating them on separate networks. While this minimized the risk of unauthorized access to physical and logical systems, the approach is becoming unsustainable. Industrial operators are connecting previously isolated assets and their data, linking them to applications running elsewhere in their domains and with the cloud, creating complex interactions that cannot be reconciled with closed architectures or system isolation. With vital systems connected, we need to take steps to create secure environments and mitigate growing vulnerabilities.
Security Gone Wrong
Beyond understanding the value that cybersecurity brings in protecting critical systems and information, the IT departments and decision-makers who deploy these solutions must understand how each design consideration affects their systems' security and operation.
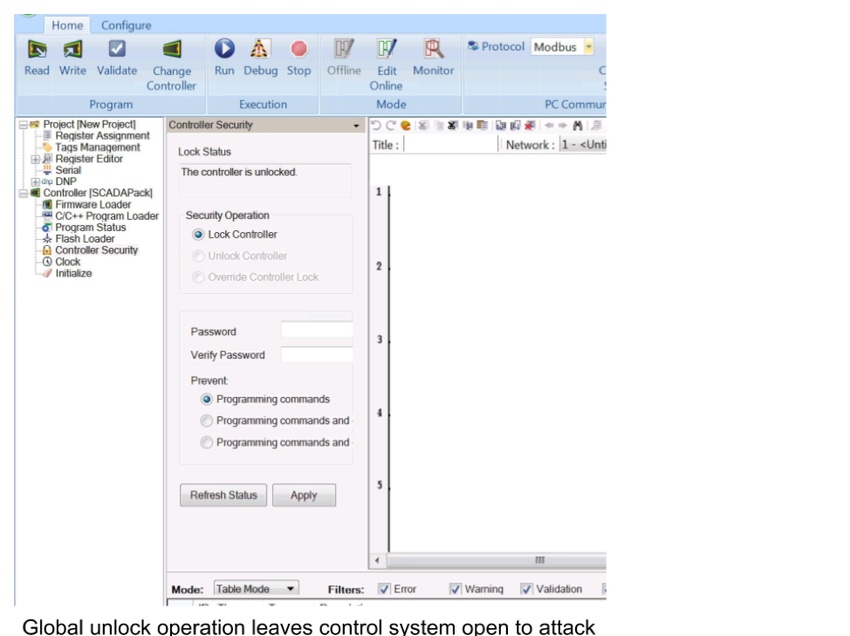
To demonstrate the importance of security design, let's walk through a common setup in major industrial operations: a Windows computer with a programming application that accesses an industrial programmable logic controller (PLC). The following two examples are specific security features that are frequently deployed with good intentions. Yet these solutions fall short in the face of today's multifaceted landscape of risks.
Scenario 1: Locking a PLC
One of the most popular PLC models enables the user to "lock" the PLC, as you would lock your personal cellphone. Only users who know about the PLC and its passcode can unlock it. This seems like a logical solution to ensure that the device is inaccessible to unauthorized parties.
However, the moment that particular PLC is unlocked, anyone who is on the broader system's network has access to the PLC. For instance, anyone could use the PLC vendor's programming software to connect to the PLC in question.

Unencrypted, easily stolen, unlocked password passing over network.Source: Susanto Irwan
Scenario 2: Locking the Software
A step up from locking a PLC is locking software itself. One of the most popular programming software suites offers the ability to lock access to that software, preventing unauthorized users from making changes in code that affect the system or other devices.
However, this is only locally enforced, functioning within that particular software and machine where it is running. This means that a malicious user could run another instance of the same programming software on a different machine, make changes, and gain access to that PLC without authorization to do so.
Layered Security Design, Threat Modeling, and Continuous Iterations
Attackers will exploit the easiest and quickest way into a system. And in the scenarios described above, the critical missing component was secure identity-based access covering the entire system, regardless of device or software.
Just as anyone on a network has access to an online PLC, they also can lock the PLC — without having to authenticate the person applying the lock. As a result, a malicious user or malware can lock a PLC, then hide or discard the password. Blocking all non-malicious users' ability to access that device, they then have free rein to use it to distribute ransomware. When access is based on device or memory of a specific passcode, it becomes easy to obtain or leave in plain sight for external parties to exploit.
These security measures might have been designed with the best intentions but can easily backfire, shutting down industrial operations and costing millions of dollars in lost production (and worse, havoc wrought on the system). In both scenarios, the neglected steps to thwarting malicious actors were 1) continuously iterating the security design, 2) implementing threat models, and 3) applying layered security. And to cover all the necessary ground, security solutions must be built from the ground up around universal, role-based access.
A New Architecture
Organizations must define their security policies in accordance with the risks at hand for their systems and operational scope — e.g., what are my requirements for credentials and access if there are hundreds or thousands of devices and employees logging in to the network every day? — before designing and developing their security functions. From there, it is imperative to rigorously test these functions across both static and dynamic threats, zero-day attacks, and various means of penetration from unauthorized third parties. These diagnostics can thus feed into an ongoing model of the threats at hand, and inform the organization's security measures as they evolve over time.
Recommended cycle for evaluating threats and security needs, designing security functions, and deploying solutions that comprehensively protect systems. Source: Susanto Irwan
Access control for industrial devices and systems is now a fundamental component of security compliance to protect their integrity, reliability, and safe operation — and to enable IoT at industrial scale. But in industrial operations, which are physically disparate and varied in connectivity, we must move beyond one centralized security center to a decentralized model. By deploying smaller, focused devices, we can extend beyond network-level security to protect to millions of previously exposed devices and control systems at the operational edge. This increases the universal enforcement of access control, and if one device or group of devices becomes compromised, can prevent the shutdown — or devastating attack — of an entire network.
Related Content:

Join Dark Reading LIVE for two cybersecurity summits at Interop 2019. Learn from the industry's most knowledgeable IT security experts. Check out the Interop agenda here.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




