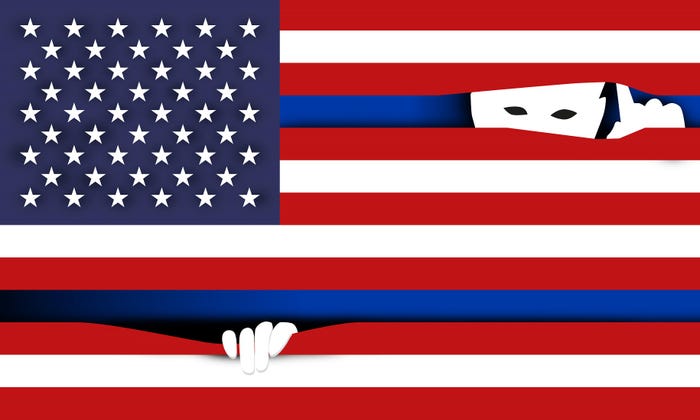
Two figures draped in US and Chinese flags confronting each other
ICS/OT Security
FBI Director Wray Issues Dire Warning on China's Cybersecurity ThreatFBI Director Wray Issues Dire Warning on China's Cybersecurity Threat
Chinese actors are ready and poised to do "devastating" damage to key US infrastructure services if needed, he said.
Keep up with the latest cybersecurity threats, newly discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or weekly right to your email inbox.






































.jpg?width=100&auto=webp&quality=80&disable=upscale)







