Three-fourths of physicians use more than one mobile device for work, a new study shows.
One in five doctors’ mobile devices are at high risk of attack, according to a new study.
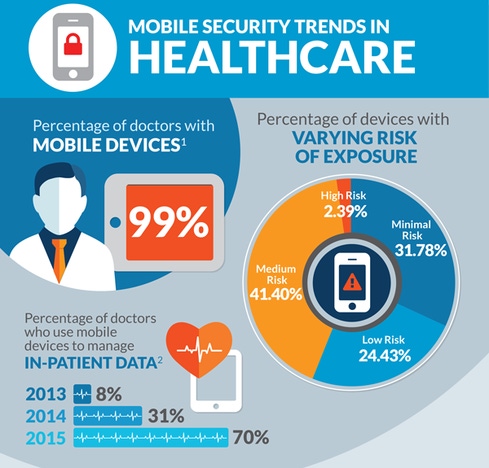
Medical professionals have become savvy tech users: 99% of doctors use mobile devices as of 2015 and the number of doctors using more than one type of mobile device increased from 28% in 2013 to nearly three-fourths (74%) in 2015. In addition, doctors are using mobile devices in a number of ways to share patient data: 46% use picture messaging, 33% use WhatsApp, and 65% use SMS or texting, according to mobile security firm Skycure's newly published Mobile Threat Intelligence report, which is based on its worldwide mobile data as well as third-party sources.
Meanwhile, healthcare organizations increasingly are becoming a popular and lucrative victim for cybercriminals. While it's not surprising that doctors like most other professionals use mobile devices to download apps and share data, it underscores the potential for exposure of sensitive medical records if those devices get compromised.
Many doctors are not adopting even the simplest security practices with their mobile devices. Some 14% of mobile devices that contain patient data aren't protected by a passcode, for instance. Varun Kohli, vice president of marketing for Skycure, says that it’s essential that doctors use a passcode on their device in order to protect patient data. “Do not have a device that is just lying open on the table. [Having a passcode]; that’s a basic thing you should do,” he says, adding that doctors should also look for malicious profiles in the settings of their devices as well as download a mobile security app for their devices.
Healthcare providers should also keep the device apps and operating systems updated against the latest vulnerabilities. “It’s not just about bad guys and bad apps,” he says. "It's about good apps with holes.”
The report also found that 27.79 million devices running medical apps might also be infected with a high-risk malware.
But that doesn't mean doctors shouldn't be able to use mobile devices at work. “To be clear, the real risk here is improperly secured devices that may be physically lost or stolen. Mobile malware and remote exploitation of mobile devices can be a risk to [protected health information] PHI, but those kinds of attacks are not commonly seen in the wild and are becoming less and less common as mobile devices become increasingly hardened," says Jon Oberheide, CTO of Duo Security.
Skycure's Kohli also doesn’t believe in stripping the healthcare industry of its BYOD. “Don’t focus on not allowing employees to use devices and apps,” but rather focus on visibility, he says. “If you don’t even know how many of your devices were attacked, how can you know where the attacks are coming from?” asks Kohli.
Healthcare professionals also should be aware of the types of cybercrime affecting the healthcare industry. “We’re only seeing the tip of the iceberg,” says Kohli, noting that ransomware attacks are becoming a major issue for hospitals as well.
In light of the latest news that two more hospitals were struck by ransomware--in California and Indiana--Ellen M. Derrico, senior director of global product marketing, Healthcare & Life Sciences for RES, says that when it comes to ransomware, healthcare organizations should focus on users. “In healthcare environments, there is a crucial need for context-aware tools and solutions to aid the very mobile physician at the point of care. The best approach is to have technology that can protect, keep itself abreast of software updates, plan ahead with back-up and recovery processes and help the organization to stay educated on potential security threats," Derrico says.
Meanwhile, healthcare professionals should try to get ahead of the bad guys and secure their mobile devices before they become major targets. “Mobile devices are gold mines [for cybercriminals]," Kohli says.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




