Whether you’re Lord Commander of the Night’s Watch or the CISO of a mainstream business, it’s not easy to defend against a constantly evolving threat that is as deadly as an army of White Walkers.
**Warning - potential spoiler alert**
The popular Game of Thrones series starts with the ominous warning that “Winter is Coming” and in the mythical Westeros, children are raised hearing stories of "the Long Night," a winter that happened thousands of years ago and supposedly lasted a generation. It was during this Long Night, that man first encountered the White Walkers, an ancient race of ice creatures looking to devour all things good and cover the lands in ice and snow.
In the far less fantastic world in which you and I live today, there is also a growing threat. Like the White Walkers, this threat is the subject of countless stories which haunt the nightmares of modern CISOs: security breaches. Before you scoff, let me point out that mega hacks like Target and Home Depot were so serious that every day non-security people changed their buying habits. The repeated occurrence of huge, public data breaches, the increasingly stringent compliance regulations, and the brand reputational damages associated with breaches are just a few of the things that have elevated cybersecurity from an afterthought to a board-level discussion.
Even scarier, like the White Walkers, security breaches and the hackers causing them show no sign of going away.
Of the many qualities that make the White Walkers such formidable opponents, one stands out as the most impactful: their ability to reanimate corpses of the dead as soldiers in their army. The ramification of this necromancy is a positive feedback loop which has enabled the White Walkers to amass a staggering number of undead troops. As their numbers swell, their ability to combat the living increases, thus producing more dead that join the ranks.
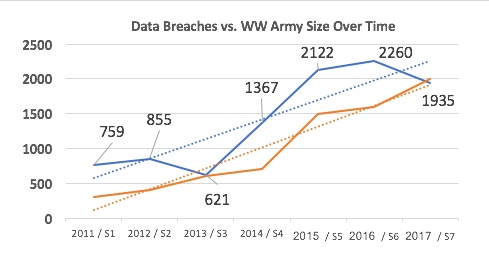
Likewise security breaches are also growing. According to data from the last several Verizon Data Breach Investigation Reports, the annual number of security breaches has grown from 759 in 2011 to 1,935 in 2017. This works out to be an average annual growth rate of roughly 22%. There are scores of factors influencing this steady rise in data breaches, among them: a growing sprawl of software available to consumers (which may potentially contain security coding flaws), the fact that more and more devices are connected to the Internet (and thus potential targets), and that human users are still the weakest link in the security equation because they often ignore 'light lifting' security measures like updating passwords.
Game of Thrones seasons one through seven conveniently line up perfectly with this period of time, so we can actually attempt to map data between the series and the DBIR report. While Verizon has a soundly scientific methodology for determining what counts as a data breach and how many occur each year, the actions of White Walkers and their undead servants are not so cut-and-dry. With that said, we do get hints about the White Walkers with each season that we can use to draw some totally subjective conclusions. And if we overlay our totally scientific data, with our wildly subjective GoT data, we get the following chart.

Image Source: Exabeam
You might disagree with my analysis of the WW army growth trends, but what I’m sure that we both can agree on is that the army is growing rapidly and poses an ever-present threat to the North. That brings me to my next point, what to do about these security threats?
Prepare for the Worst
While it might be the case that The Wall will hold off the White Walkers forever. Alternatively, it may only buy the poor folk of Westeros some time before they join the ranks of the undead. In other words, the longstanding defense mechanisms put in place by the IT security teams of yore (i.e. firewalls, access controls, WAF, etc.), might stave off cyber attackers or they might simply slow them down.
Whether you’re the Lord Commander of the Night’s Watch or CISO of a tech upstart or mainstream business, it’s your job to prepare your organization to defend itself against hackers and threats. You’ll need to understand your adversary, pool and distribute your resources, and invest in the people, processes, and technology necessary to combat the peril your organization is facing.
Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




