When harnessed properly, threat hunting can be one of the most useful techniques for finding attackers in your network. But it won’t happen overnight.
The terms “threat intelligence” and “threat hunting” have become the next big thing in information security over the last few years. While many researchers (including myself) still view these buzzwords unfavorably, the reality is that – when done correctly - the concepts, processes, and strategies are critical to the security of an organization.
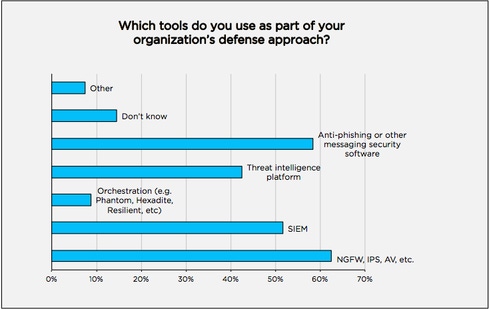
According to recent "report card" research from DomainTools, over 40% of survey respondents said their organization currently uses some sort of threat intelligence platform. This demonstrates that the field is growing - and with a heavy focus on threat hunting. The report card examined the maturity of information security departments across the globe, and gauged their success in implementing hunt capabilities in both small and large organizations.
But What Is Threat Hunting, Really?
It’s important to remember that threat intelligence is merely threat data with contextualized analysis to help analysts understand the threats to their organization. Threat intelligence isn’t as easy as merely paying for an API or web portal to access specific threat data. Performing proper threat analysis requires skilled analysts, vetted information and data, timely information, and multiple data sources.
Often over-used and misunderstood, threat hunting is the process of proactively searching through networks and host data to detect and possibly help eliminate miscreants from networks and hosts. Performing one hunt can be different from another, and hunts vary from analyst to analyst. Many good hunters define their ability to hunt as an art versus a science. Many hunters rely on gut feel in conjunction with proper security analysis platforms, therefore combining the art and science of hunting. Unfortunately, hunting is often seen as hugely beneficial, but difficult to implement.
A-Hunting We Will Go: Threat Hunting Maturity
In our research, we found that threat hunting is emerging as a top tactic among many organizations. Of the respondents, more than one quarter (26%) indicated they spend 26 hours or more per week hunting threats in the network. A large majority (78%) of respondents using hunt capabilities find value in hunting – specifically drilling down on forensic clues from emails, such as domain name, IP address, or email address, which ideally leads to information that makes the organization more secure. Many of these organizations then take the information they find to proactively block on their proxies/egress firewalls and other defensive technology. Some of those same organizations will actually share out indicators of attack (IOA) or indicators of compromise (IOC) to like industries.
It Takes Time to Get it Right
Standing up a threat hunting capability doesn’t need to be difficult, but it needs to be right. The speed of adoption of a hunt program is one of the biggest and most prevalent issues I’ve witnessed within organizations attempting to stand up a hunting program. It takes time to implement and properly run a threat hunt team or capability! One of the most important things an organization should consider at the outset is the Threat Hunting Maturity Model from SQRRL.

Source: SQRRL Threat Maturity Model
By following this maturity model as a foundation for your own hunt capability, you can work your way through the four levels it takes to grow hunt capability organically – helping reduce the pains commonly associated with a developing hunt program. In addition to the maturity model process, it’s also important for organizations to have proper automation technology in place for when they achieve maturity.

Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




