Data leakage and corruption haunt iOS and Android mobile apps the most, a new study shows.

Apple's iOS mobile platform suffers fewer cyberattacks than Google's Android, but a new study shows that when iOS does get hit, the attacks are more severe.
Pradeo's biannual mobile applications threat review report, released today, examines the mobile threat landscape based on a recent portion of the 1.5 million single applications processed by the firm. "What is interesting is that the iOS does not have the same degree of problems as Android," says Vivien Raoul, Pradeo's chief technology officer, of the findings. "Although it comes less often, it is generally more of a serious problem that affects the system itself."
The iOS system after downloading an app asks the user each time if he or she wants the app to access their personal databefore allowing that task to launch, while Android just automatically launches once the app has been downloaded, Raoul explains.
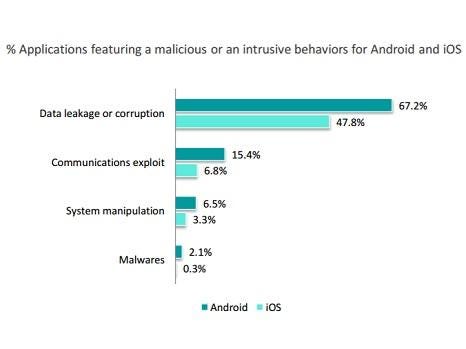
A compromised iOS system can allow data leakage and corruption to occur, he says. According to the Pradeo study, data leakage and corruption affect 47.8% of iOS applications that carry malicious or intrusive behavior.
 [Source: Pradeo]
[Source: Pradeo]
When it comes to all mobile applications with malicious intent or intrusive behavior, data leakage or corruption is by far the worst for both iOS and Android, accounting for 60.7% of the cases, according to the study. Communications exploits represented 12.5% and system manipulation 5.5%. Malware, however, accounts for only 1.5%.
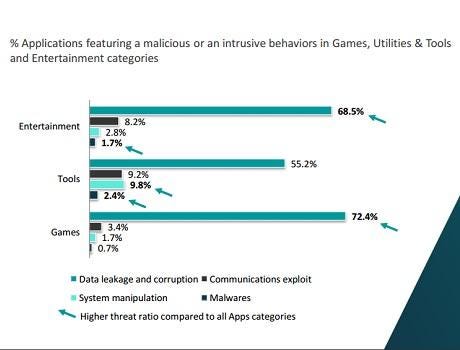
That ranking also largely held true among the most popular applications – games, entertainment, and tools. The only exception is tools, where system manipulation has a higher occurrence frequency in those apps than communications exploits.
 [Source: Pradeo]
[Source: Pradeo]
For Pradeo's Raoul, one of the more surprising figures in his firm's report was the degree that zero-day threats are growing. Applications embedding unknown malware threats have quadrupled over the past year, the study shows.
"There are new techniques every year and the attackers have a huge imagination," Raoul says.
The study also found that 25% of mobile applications carry vulnerabilities, of which 75% of these flaws are among the top 10 Open Web Application Security Project (OWASP) vulnerabilities.
"The top 10 OWASP are critical vulnerabilities, but in most cases, these vulnerabilities will affect the performance of the app and not the device or system," Raoul explains. As a result, companies may not be quick to patch these vulnerabilities on their company owned smartphones or nudge their BYOD workers to install an update patch.
Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




