Recent high profile attacks reflect a new reality in which perimeter-based security models are increasingly less effective in protecting key corporate assets and information.
Over the past 18 months, many corporations have been forcefully introduced to a new era of highly visible security events, from large scale Distributed Denial of Service (DDoS) attacks to social media account takeovers. To those outside the security community, this may feel like a sudden assault on the world’s organizations, but these attacks are merely the tip of an iceberg that has been growing inside enterprise networks for more than two decades.
What lies beneath
Since businesses first opened up their networks with Internet gateways in the early 1990s, we’ve seen security administration become increasingly distributed, enterprise perimeters become less effective, and frantic protections impede user experience. For organizations realistic enough to accept that their perimeter no longer protects key assets and intellectual property, there is a new model for enterprise security that brings together mobile devices, identity and access management, virtual private networks, and cloud infrastructure.
However, this new model requires security teams to rethink their reliance on traditional firewalls and adopt a new paradigm better suited to protecting against ever more sophisticated and stealthy threats such as Advanced Persistent Threats (APTs). Audits and certifications will also have to be redesigned and businesses will need to prioritize their protection decisions.
Management priorities
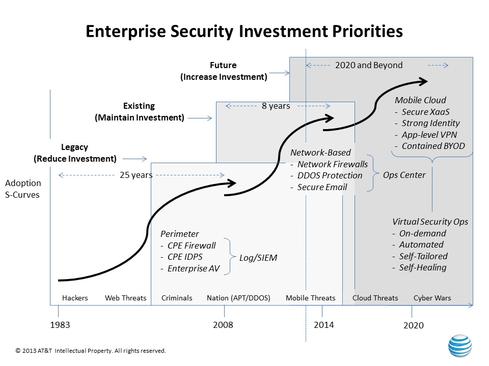
Understanding where to reduce, maintain, or increase security investments will be critical to mounting an effective defense against the next evolution of threats. Reducing investments in legacy systems, including perimeter-based firewalls, untethers essential resources that support the trajectory of today’s business transformations into mobile and the cloud. Maintaining existing protections while transitioning to advanced architectures is important, but adding more sandbags to traditional perimeter strategies will provide limited return.
The challenge, then, for senior management and audit teams, is to focus protection efforts on the most critical resources. But this strategy will require a major change in thinking since the most basic tenet of today’s corporate audit involves testing controls to ensure 100 percent compliance with corporate policy. This mentality needs to change so businesses can prioritize investments on protections that will yield the best possible security posture. Forward-thinking security teams are already heavily invested in network-based protection, and are increasing investments in virtual security operations.
Securing mobile business
For now, the most pressing security needs for most businesses include the rise of BYOD, mobile threats, and the cloud. Other threats include the ever-increasing sophistication of DDoS attacks and APTs. Network-based protections, also known as cloud-based protections, are minimal defenses against all of these threats because of the network visibility required to detect and mitigate them.
With the network as the foundation, security teams can then create security “zones” to provide customized levels and types of protection for each asset based on its individual risk profile. For example, access to an asset categorized as high risk could require device level controls, multi-factor identity authentication, VPN/secure tunnels, and API verification. Access to a low-risk asset could be managed with fewer controls.
Look up to the cloud
The future of cybersecurity will be virtualized, moving management and threat detection to the cloud. When deployed properly, the cloud provides several critical security advantages over perimeter-based models including greater automation, self-tailoring, and self-healing characteristics of virtualized security. In this new architecture, identify and access management should be viewed as primary controls enabling the cloud to become the platform for enterprise security. This approach allows security teams to decouple security software from hardware and deliver on-demand protection rapidly and flexibly via APIs.
Do you see the demise of traditional perimeter-based security in your organization any time soon? Let’s chat about what that will mean in the comments.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




