New technologies like software-defined segmentation are making it easier to prevent a compromise from spreading by separating users and network resources into zones.
Cybersecurity panic seems to be on the rise in 2015. Hacked cars, compromised healthcare records and one of the largest breaches in U.S. history have left many people wringing their hands in anxiety.
This scenario reminds me of the reactions to the large fires of the industrial revolution and the changes that happened afterward. In 1871 a fire broke out in Chicago, America’s fastest growing city at the time. Aided by high winds, the fire jumped from building to building until roughly one third of the city was destroyed. The event received immense media attention, and large-scale fires would later affect other urban centers such as London and Boston.
At the time, many criticized the rush to industrialize or blamed the catastrophe on divine retribution for a lack of morality – sound familiar? Despite the panic, the ultimate solution to the problem was constructing buildings a little farther from each other, utilizing flame-resistant materials and implementing quick response to fires. Fire codes are meant to create an environment that limits the spread of a fire, and the concept is equally effective when applied to network security.
In many networks, there is little stopping an attacker from accessing everything once they are inside. Like a fire, they spread from area to area until nothing is left and all of the data is compromised. Network segmentation is akin to bringing your network up to code. By separating users and network resources into separate zones, it prevents a compromise from spreading. And just as the invention of automatic sprinklers and quick response systems made firefighting more effective, new technologies are making segmentation easier, smarter and more dynamic.
A new era of segmentation
In an unsegmented network, everyone can access everything. Engineers can access financial records, legal can access proprietary technology, and even third party contractors are sometimes given complete system access. While this may be convenient from an employee standpoint, it is a nightmare for security teams. All attackers have to do is subvert perimeter defenses – something they have become incredibly skilled at – and they have access to everything and the kitchen sink.
Network segmentation has been around for a long time, but many organizations have forgone implementing it because traditional methods have some key shortcomings. The main challenge of conventional network segmentation is that it is impractical to implement and maintain in large corporate environments. Traditionally, it requires the maintenance of extensive access control lists, which have to be updated across many different points of enforcement whenever a change occurs. In networks with thousands of users and multiple environments, such as the cloud and specialized IoT networks, this quickly becomes nearly impossible to manage.
Also, traditional segmentation offers no practical way to monitor the effectiveness of policies. Identifying a misconfigured policy that allows traffic between zones that should be separated was difficult and adjusting it was time-consuming.
Software-defined segmentation has come a long way to address these issues. By abstracting access control and assigning it to user and machine identity information, instead of ever-changing IP addresses, management is much more intuitive and responsive. In addition, centralizing policy management and automatically pushing updates to all points of enforcement drastically reduces maintenance time and maintains policy integrity networkwide. Software-defined segmentation is better suited to controlling access in virtualized and cloud environments as well.
Every segment traversed is an opportunity to monitor and govern traffic. Having tools to model, validate and then segment the way in which your organization operates is the practice that will get us from the past to the future of network design and operations – the new methodology.
New segmentation needs new methodology
Even with all of the advantages of software-defined segmentation, there still exists the problem of intelligently crafting segmentation policies. Improperly designed policies can create security risk or cripple business functions by denying legitimate insiders access to critical resources.
To take full advantage of software-defined segmentation, a smart implementation and maintenance methodology is needed. Security architects can utilize the process of active segmentation to ensure proper segmentation is maintained without disruption to day-to-day business.
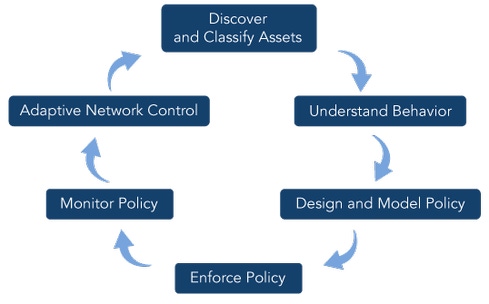
Like all great approaches to cybersecurity, active segmentation is a cyclical process that involves observation, orientation and adaptation to changing circumstances and environments. When used properly, active segmentation consists of:
Inventorying network assets and classifying them based on role or function
Gaining insight into user behavior and interactions on the network
Intelligently designing segmentation policies based on those insights
Enforcing the policies
Continuously evaluating policy effectiveness
Adjusting policies where necessary
One of the prerequisites of active segmentation is end-to-end network visibility. Without the ability to monitor network behavior and identify traffic patterns, crafting an effective segmentation plan is simply too difficult. You need to be able to inventory network assets and understand how users interact with them to avoid creating improper segmentation policies.
Using network visibility and monitoring tools, active segmentation provides two primary benefits:
First, administrators can model segmentation policies before implementing them. As users continue to operate normally on the network, any violation of proposed segmentation policies will trigger an alarm. This way, administrators can identify any business disruptions that might occur and adjust the model accordingly, which in turn makes the implementation of segmentation smoother.
Secondly, continuing to monitor the model allows for continuous evaluation of policy effectiveness. If a user violates intended segmentation, alerts are triggered and administrators can investigate and reconfigure the policy as necessary. New network hosts and systems can also be quickly identified and assigned the appropriate privileges. This approach ensures segmentation is properly maintained as the network grows and changes.
Bring your network up to code
As the threat landscape continues to evolve, network defenders need to give themselves as much leeway as possible. Similar to modern fire prevention, you cannot stop an event from ever happening, but the right amount of preparation can keep a small house fire from burning down the rest of the city.
Network segmentation has always been an important defensive measure, but it wasn't until recent technologies were developed that it could be effectively deployed in large enterprise networks. Software-defined segmentation facilitates adaptive segmentation in large environments, but it doesn't get rid of the guesswork. Instead of designing policies based on intuition alone, security architects should utilize active segmentation to ensure their policies are crafted intelligently, based on real-world observation and monitored for effectiveness.
Just as fire codes help prevent catastrophes, active segmentation can severely limit the reach of a breach and improve an organization’s security posture.
Read more about:
Black Hat NewsAbout the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




