Not surprisingly, our latest poll confirms that threats stemming from criminals hacking humans are all too frequently ignored.
When it comes to social engineering, Pogo, the central character of a long-running American comic strip, said it best. "We have met the enemy and he is us."
It was 1971 when Walt Kelly penned the cartoon with the celebrated quote; Pogo, who lived in a swamp, was talking about Earth Day. Today, the same sentiment can be applied to employees who are blissfully ignorant of the lengths criminals will take to gain their confidence in order to breach an organization’s security and steal proprietary data.
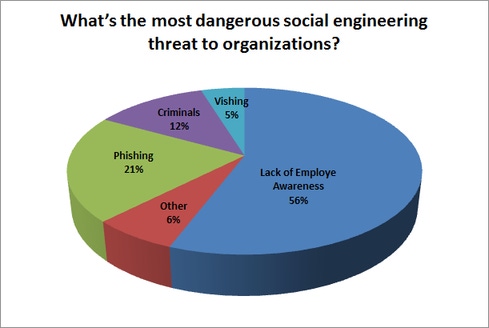
But don’t take my word for it. According to a recent Dark Reading flash poll, more than half of 633 security professionals who responded said that the most dangerous social engineering threat to their organizations was due to a lack of employee awareness.
Email phishing scams were specifically identified as serious attacks by 22% of respondents, followed by criminals posing on site as contractors or employees (12%). “Vishing,” a relatively new but growing scheme in which people are tricked into revealing seemingly innocuous information over the phone, was reported by only 5% of poll takers.
The Dark Reading community poll data is in direct contrast to today’s increasingly sophisticated methods of socially-engineered hacking. To combat those threats, says Chief Human Hacker Chris Hadnagy, a social engineering expert and author from Social-Engineer.com, security professionals need to redouble employee awareness efforts around new trends in phishing and multi-stage attacks.
“Phishing emails are much more complicated today ... and [phishers] are using spell check!” Hadnagy said during a recent Dark Reading Radio show, noting that “serious phishers” are hiring proofreaders as a customer-service option to delivers “branded, well-written phishing emails that are really working.”
In multi-stage attacks, he says criminals use both phishing and vishing to gain the trust of individuals who give attackers a foothold into corporate networks and systems. “Fifteen seconds after they send you a phishing email, they will call on the phone and ask you to click on the link that causes systems to crash.”
Hadnagy, whose company hosts the annual Social Engineering Capture the Flag contest at DEF CON, said a blend of education and technology is the best solution to the problem. “Yes, have your AV's, IDS, IPS, packet inspection, etc. all set up. But don't rely on tech to save you from the human element. Mix both education and tech to get the biggest benefit.”
As for what kind of education, he said what works best is when training is combined with a real-world example. Employees, for instance, receive a test phishing email, and those who fail the test and click on a link are immediately dispatched to a page with information about the dangers of phishing. The quick lesson is later followed up with more in-depth training.
For more details, check out the How to Hack a Human radio show interview and chat with Chris Hadnagy and Dark Reading Executive Editor Kelly Jackson Higgins.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




