Cybercriminals targeting financial institutions in the UK bypassed Symantec email gateway and other perimeter technologies.
A newly discovered phishing campaign aims to slip past perimeter security tools by using SharePoint to send malicious documents to victims primarily in the UK financial services sector.
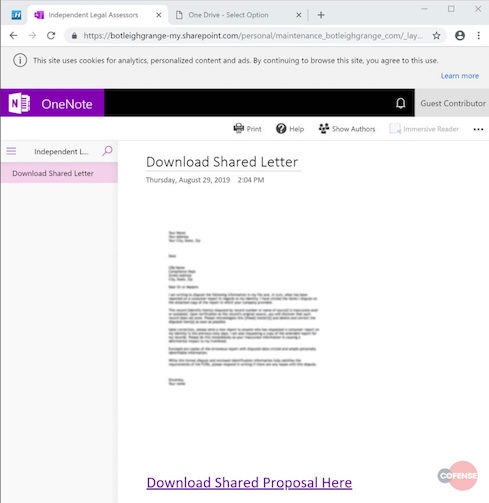
Researchers with Cofense who disclosed the attack say the initial email comes from a compromised account belonging to Independent Legal Assessors, a legitimate legal services firm based in London. Recipients are asked to review a proposal document by clicking a URL embedded in the email, which redirects them to a compromised SharePoint account.
SharePoint serves as the initial mechanism to deliver a second malicious URL. Victims who access the compromised SharePoint site will see a malicious OneNote document, which they are prompted to download. This secondary step takes them to the main credential phishing page, which is "a cheap imitation" of the OneDrive for Business portal, researchers explain. Victims have two options to authenticate: either by using Office 365 credentials or a username and password for another email provider. The second increases the chance someone will log in.
Many automated defensive tools only go one layer deep, explains Cofense CTO Aaron Higbee. Because the first embedded URL comes from SharePoint and the email doesn't contain malware, it's not flagged as a threat. In Cofense's example, attackers wrapped the URL with Symantec Click-time URL Protection, but this tactic can be used to bypass many perimeter tools.
"A few years ago, we would've found it, but now the attackers use one layer to link you to another website," Higbee says. Most of the attackers' emails contain typically office communications. Some discuss legal summons or issues; others relate to billing and invoices.
Researchers downloaded files from the compromised server and found that credentials from the phishing form are posted by login.php, which posts harvested credentials via email to [@]gmail[.]com. Researchers assume [@]gmail[.]com is a separate compromised account. Other files from the server could point to the origin of the attack. Researchers discovered a readme file providing the operator with instructions on how to configure and install the phishing page onto a compromised server. The phishing kit is built and sold by BlackShop Tools, researchers explain in a blog post on their findings.
This campaign is the latest instance of an increasingly popular trend. Attackers use services like SharePoint, OneDrive, and Windows.net as intermediaries to redirect people to phishing sites. It poses a tremendous challenge to defenders, who don't have the option of blocking them.
"When your own business is on Office 365, you can't necessarily block these cloud domain names," Higbee says. "This one was SharePoint, but we are seeing the entirety of the Office 365 suite being abused quite frequently from attackers." Microsoft's Office 365 is used far more often in these types of phishing attacks compared with Google's G Suite, he adds.
While these attacks may present a red flag in the form of an unusual URL on the OneDrive portal, Higbee points out these may not be noticed on smartphones, which unlike desktops don't visibly show the URL bar. "You know how impractical that is on a mobile device," he says, noting that it "would be very difficult for someone to key in on this."
Check out The Edge, Dark Reading's new section for features, threat data, and in-depth perspectives. Today's top story: 'It Takes Restraint': A Seasoned CISO's Sage Advice for New CISOs
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




