Packet sniffing, drones and cat memes. And the winning caption is….
May 3, 2016
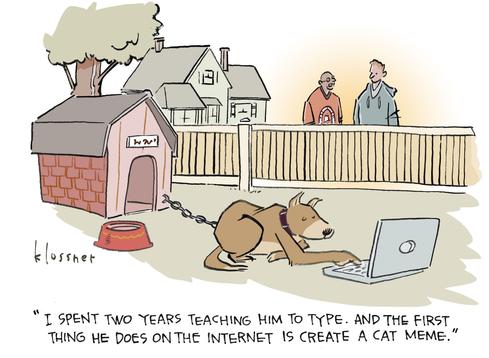
There’s no shortage of dog lovers (and cat puns) in the Dark Reading community! This month’s cartoon contest entries – 81 in all -- offered more than a few laugh-out-loud moments for the 2,500+ readers who kept tabs on the captions as they poured in.
And so, without further ado, the winning caption...
First-prize winner ioshield takes home a $25 Amazon gift card and his much-deserved moment of fame in the final version of the cartoon by John Klossner, who helped judge the contest along with the Dark Reading editorial team: Tim Wilson, Kelly Jackson Higgins, Sara Peters, and yours truly.
The competition was stiff! We also awarded two honorable mentions (and $10 Amazon cards) to Stephen McCallister, (aka smccallister), of Stephen R. McCallister HIT Consulting, for:
"He's on Facebook again, no one's ever going to convince him 'Who Let the Dogs Out' is a rhetorical question.”
And to awperkins04 for:
"We got him as a security dog, and he's surprisingly good at it, though we would still prefer him to bark at intruders as opposed to sending them menacing emails."
Thanks again to everyone who entered the contest. If you haven’t yet read all the captions, be sure to check them out today.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024