Chief information security officers are considered 'accountable' for breaches while not always in charge of all infosec strategy and purchases, new report shows.
July 21, 2015
The chief information security officer (CISO) still isn't getting the respect or power necessary to do his or her job, a new report finds.
Nearly half of US CEOs and other C-level executives at US enterprises say CISOs should be held responsible when a data breach occurs, yet just 38% say CISOs should head up security strategy and purchasing decisions in their organizations. So a CISO can be a scapegoat even without the full authority to direct his or her company's security.
"It [the CISO job] comes with great responsibility, but they just forgot to give them the power," says Stuart Itkin, senior vice president at ThreatTrack Security, which conducted the study of C-level executives at 200 US companies with CISOs. "It's because the CISO role is new and evolving. There's no universal CISO job description," which makes it difficult to get the job on the same page at all organizations, he says.
Two-thirds of execs don't believe CISOs should have a seat at the table of top-level leadership in their organizations. "So the CISO isn't involved in conversations or discussions around operations and planning … and not involved in setting company strategy. That's a challenge in security if you're not party to those decisions," Itkin says.
Some 56% of the organizations in the study say their CISO reports to the CIO, and 41% say to the CEO. There was a slight uptick from last year's survey -- from 18% to 21% -- of execs saying CISOs should mainly be an advisor to IT and the CIO in security and purchasing decisions.
And only half of the organizations in the survey say CISOs "provide valuable guidance to senior leadership related to cybersecurity” -- a decline of 1% over last year. Just 10% gave their CISO a grade of an A, down from 23% last year; 45%, a B; 34%, a C; and 11%, a D.
Interestingly, the toughest graders were in industries hit hardest by breaches over the past year: retail, financial services, and healthcare, suggesting the CISO indeed is blamed when attacks occur.
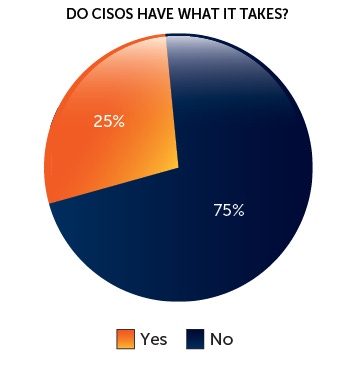
One-fourth say CISOs "greatly" improve day-to-day security practices while 19% say their CISO's decisions are detrimental to the business. Some 20% say their CISO "has yet to make a decision."
But the relative lack of respect for CISOs may merely be a natural evolution: "The CIO not too long ago" was in the same boat, notes Itkin. "We're seeing the same evolution with the CISO role. It's a new role and organizations don't understand as a whole what that role needs to be."
Meantime, there's a natural inherent conflict between the CIO and CISO. CIOs come from the IT productivity and profit side of the house, while CISOs are all about protecting and locking down corporate data, goals that can naturally collide.
"The CIO is trying to implement the best technology that is secure enough and will be cost effective," said Rick Howard, chief security officer for Palo Alto Networks in a Dark Reading Radio show last year. "The CISO sees danger in every dark corner."
The takeaway for CISOs from the new survey? "They need to manage expectations" in their organizations, Itkin says. "A lack of consensus across organizations around the CISO's role and responsibility and authority means opportunity for the CISO to manage and define those expectations across the organizations. Ensure that responsibilities in their span of control are aligned."
There's plenty of room for CISOs to evolve and take their seat at the C-level table, he says.
In an odd twist, the 62% of the execs in the survey say their CISO would be successful in a leadership role outside of IT security.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


