Attempted malware infections against BYOD and corporate mobile devices are expected to continue to grow, new data shows.

Every business with BYOD and corporate mobile device users across the globe has been exposed to mobile malware, with an average of 54 attempts per company played out within a 12-month period, according to a Check Point report released today.
The study, based on data collected from Check Point SandBlast Mobile deployments at 850 organizations, is the latest sign of growth in mobile malware incidents.
"100% of businesses [facing an attempted attack] was not surprising because the statistics from a year or two ago started to show it was going this way," says Michael Shaulov, head of Check Point's product management for mobile and cloud security. "But the average of 54 [attempts] was surprising. I was expecting two, three, or four."
The report also notes that 94% of security professionals anticipate actual mobile malware attacks to continue to increase, with nearly 66% doubting they can prevent them.
"We've seen a steady parade of malware specimens over the last several years," says James Plouffe, lead solutions architect at MobileIron. He notes although the 100% mobile malware figure seems high at first blush, it is important to distinguish between organizations that have been exposed to malware versus actually getting infected.
Patrick Hevesi, a Gartner analyst, anticipates a continued rise in mobile malware incidents and breaches. "There are billions of mobile devices for the attackers to try and gain access and some form of monetary gain," he says. "I feel as more and more people continue to make phones and tablets their primary device, the attacks will continue to grow."
Attack Drivers
Most of the malware that BYOD and corporate devices encounter comes from apps at third-party stores, Shaulov says.
Other forms of malicious activity against these devices are also taking place with great frequency. The report reveals 89% of organizations experience a least one man-in-the-middle incident stemming from users connecting to a risky WiFi network. "Attackers are trying to get access to the data transmitted, rather than inject malware," Shaulov says.
Phil Hochmuth, an IDC analyst, says BYOD devices are usually more susceptible to attack than corporate devices because they are not managed by such security measures as an enterprise mobility management platform or mobile threat management platform. These platforms can restrict some of the more liberal permissions and user settings on BYOD devices, he adds.
"We've seen mobile threats become more elaborate and go beyond malware or bad apps," says Hochmuth. "They use a mix of network-based attacks, like spoofed WiFi, or malicious management profiles to steal data. Attacks on the core mobile OS kernel, iOS and Android, are also becoming more sophisticated."
Mobile malware, for example, is also showing up pre-installed on some of the smartphone brands or embedded in apps in app stores like Google Play and Apple's App Store.
And while the report notes 75% of organizations average 35 rooted or jailbroken devices on their networks, Shaulov does not attribute that to the high percentage of companies exposed to malware. "People with jailbroken or rooted devices are power users and these are the guys who know what they are doing and are less susceptible to attacks," he says.
By industry, the Check Point report shows that financial services industry encountered the most mobile malware incidents, 39%, followed by government, 26%.
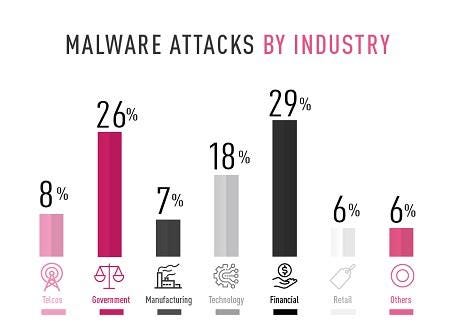 [Source: Check Point]
[Source: Check Point]
Financial services devices also took the brunt of the various mobile malware types that surfaced, according to the report. Their devices accounted for:
44% of all detected remote access Trojans (mRATs)
40% of rough ad networks that run in the background and click on ads
32% of information stealers
But when it comes to premium dialers, government-issued phones and government employees' BYOD devices were exposed to 43% of this type of malware. "Many of these premium dialers are related to phishing attacks and government employees, in particular, were more susceptible to phishing attacks," Shaulov says.
Related Content:

Join Dark Reading LIVE for two days of practical cyber defense discussions. Learn from the industry’s most knowledgeable IT security experts. Check out the INsecurity agenda here.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




