McAfee researchers have found more malware hiding in the Google Play store that is targeting North Korean dissidents. It's the second instance of the so-called ‘Sun Team.’

For the second time this year, researchers at McAfee Labs have found malware hiding in the Google Play store that seems to target North Korean dissidents by attempting to plant spyware on their Android mobile devices.
This latest incident, along with a similar discovery in January, appears to be related to the so-called "Sun Team," which has only been active for the last few years and whose origins remain unknown, according to McAfee. (See McAfee: Attackers Targeting North Korean Dissidents, Journalists.)
The latest case, which McAfee detailed in a May 17 blog post, was dubbed RedDawn, and was discovered before it could spread extensively throughout the Google Play store. McAfee alerted Google to the malware and company has since removed the apps. Only about 100 infections were discovered.
Once installed, the malware can copy personal photos, contacts, SMS messages and other information from mobile devices and send that data back to the attackers.
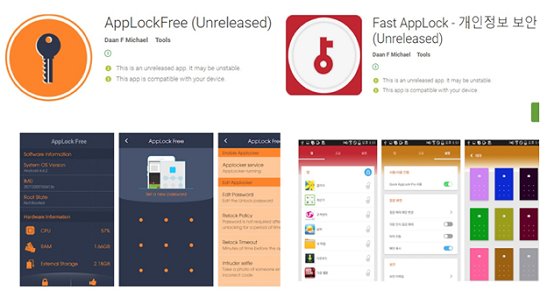
Malware uploaded on Google Play
\r\n(Source: McAfee)\r\n
In this case, the McAfee team found three infected apps. The name of the first translates to Food Ingredients Info, offering information about food, while the other two, Fast AppLock and AppLockFree, were security related.
All three worked slightly differently, but the results were the same. Fast Applock, for example, steals device information and also receives commands and additional executable (.dex) files from a remote cloud server controlled by the Sun Team.
Once installed, the malware can spread to friends of the victim, asking them to also install one of the malware-infected apps or offering fake feedback through social media, most likely Facebook. Here, too, fake profiles, which are based on stolen identities, helped promote the apps.
After the device is infected, the malware uses Dropbox or Yandex to upload data and issue commands. Within these cloud storage sites, researchers found information logs that Sun Team used during the first attack in January.
The question remains who is behind Sun Team? While the easy conclusion is to point to the North Korean government, since the malware targets dissidents, McAfee has yet to draw a definitive conclusion. Even the presence of a North Korean IP address isn't enough at this stage.
"In our post of the earlier attack by this actor, we observed that some of the Korean words found on the malware's control server are not in South Korean vocabulary and that an exposed IP address points to North Korea. Also, Dropbox accounts were names from South Korean drama or celebrities," according to Thursday's post, meaning that the Sun Team has knowledge of Korean culture.
Earlier this year, McAfee published a report about mobile attacks increasing as more and more devices come online and attackers use increasingly sophisticated techniques to spread malware.
Related posts:
— Scott Ferguson is the managing editor of Light Reading and the editor of Security Now. Follow him on Twitter @sferguson_LR.
Read more about:
Security NowAbout the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




