Critical vulnerabilities, links and virtual reality. And the winner is...
August 12, 2016
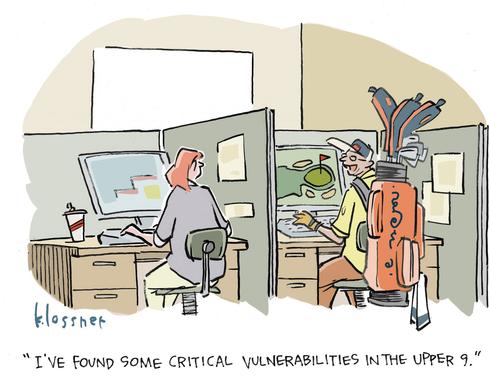
Pokemon Go may have been all the rage this summer, but for Dark Reading’s wanna-be cartoonists the birdie that took the honors involved word play on golf, vulnerabilities, and virtual reality! So without further ado, kudos to our first place winner jeberha3 for the caption, penned by cartoonist John Klossner below:
Jeberha takes home a $25 Amazon gift card for this substantially above par submission. But the geeky humor and puns didn’t stop there. A grand total of 75 Dark Reading community members teed up captions for more than 2400 score-keeping readers keeping a watchful eye as the hysterical submissions flew over our virtual fairway to deliver two more holes in one.
Runners Up ($10 Amazon each):
Abby Ross – aka abby.ross -- director of public relations & marketing communications, Bay Dynamics:
"Hey Bill, did you get the report from our vulnerability scan?"
"Yep. Looking at the holes as we speak."
Gallums:
"It's a tough job but someone has to test the links."
Congratulations to all the winners and contest entrants -- and many thanks to all our Dark Readers for joining in the fun. If you haven’t yet read all the captions, be sure to check them out today.
Related content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024