Rare SMB-focused cyber espionage campaign hitting small firms worldwide.
Yet another reminder that even small companies aren't immune from cyber espionage hacks: researchers have discovered an aggressive attack campaign against SMBs around the globe that appears to be targeting the chemical, nanotechnology, education, agriculture, media, and construction sectors for intelligence purposes.
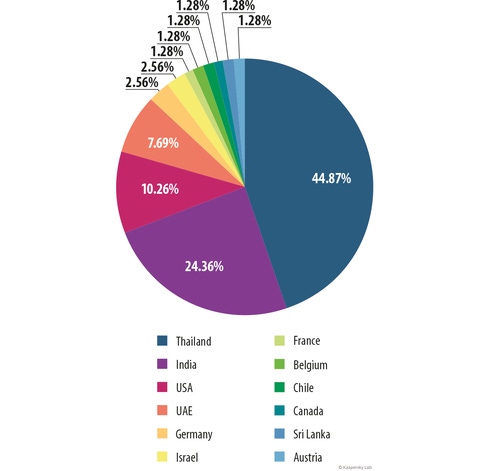
Kaspersky Lab researchers today gave details about the newly discovered Grabit malware and its attack campaign that has been underway since February of this year and remains active. The cyber espionage attack has stolen some 10,000 files from victims mostly in Thailand, India, and the US; but Kaspersky has seen victims in the United Arab Emirates, Germany, Israel, Canada, France, Austria, Sri Lanka, Chile, and Belgium.
The attackers appear to be after everything from credentials to system information. "Based on our research, we’ve seen that credentials is not the main focus and that Grabit collects internal information about the system – firewall, anti-virus installed, machine name, internal/external IPs, keylog, screenshots, machine time [and] language and more," says Ido Naor, senior security researcher for Kaspersky Lab's Global Research & Analysis Team.
Naor says he and his fellow researchers are still studying just what type of information Grabit's attackers are ultimately after. He doesn't believe the SMB targets are being used as stepping stones to bigger targets, either. "Although one victim had a very sensitive set of credentials stolen, we still haven’t seen any bridge between the SMBs and any organization that could be seen as the final targeted destination," he says.
He says it's unusual to see a cyberespionage campaign specifically targeting SMBs. "I actually haven’t seen an SMB's malware that targeted this amount of victims before. The group behind Grabit have [a] developed plan. Through our research we are doing what we can to intercept it," Naor says.
The researchers stopped short of speculating just who or what nation or region is behind the attack, but note that Thailand and India had the most infected machines overall.
The attack begins with a phishing email outfitted with a malicious Word document. Once the user opens the attachment, the malware is delivered to the user's machine via a remote (and actually compromised) legitimate server that hosts the malware, which is based on the infamous commercial HawkEye keylogger kit used for cyberspying. The attackers also deliver several remote administration tools, or RATs, to the victim.
"The decoy document is not leveraging any exploit or zero-day to bypass the victim's judgment. Instead, it waits for the attacker's call to enable the macro," he says. "This type of attack matches the victim’s profile: a manager/director, who usually opens many documents.”
Kaspersky Lab researchers found that a keylogger from one of the attacker's command-and-control servers had stolen 2,887 passwords, 1,052 email messages, and 3,024 usernames from some 4,928 different host machines at the victim SMBs. Among the booty: Outlook, Facebook, Skype, Gmail, Pinterest, Yahoo, LinkedIn, Twitter, and online banking accounts.
The attack group appears a bit scattershot, with a combination of weak security and sophisticated methods to avoid discovery, according to Kaspersky. In one case, the malware was phoning home out in the open and easily spotted. "In addition, the files themselves were not programmed to make any kind of registry maneuvers that would hide them from Windows Explorer. Taking that into an equation, it seems that the threat actors are sending a “weak knight in a heavy armor” to war. "It means that whoever programmed the malware did not write all the code from scratch," Kaspersky senior security researcher Ido Naor wrote in a blog post today.
But they also use obfuscation, strong encryption, and ASLR to make it more difficult for researchers to discover and analyze the malware. "Along with these different sizes, activities, and obfuscation, a serious encryption algorithm was also implemented in each one of them. The proprietary obfuscated string, methods and classes made it rather challenging to analyze," Naor blogged. "ASLR [Address Space Layout Randomization] is also enabled, which might point to an open source RAT or even a commercial framework that packed the malicious software in a well written structure."
There are a few ways to check for Grabit infections, according to Kaspersky: the C:\Users\<PC-NAME>\AppData\Roaming\Microsoft area of a user's machine has executable files; or if the Windows System Configuration includes "grabit1.exe" in the startup table. "Run “msconfig” and ensure that it is clean from grabit1.exe records," Kaspersky Lab said in its blog post today.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


