'Turla' exploits unencrypted satellite links in Africa and the Middle East to evade detection.
September 9, 2015
A notorious cyber espionage gang believed to be out of Russia commandeers unencrypted satellite links to mask its information-stealing operations.
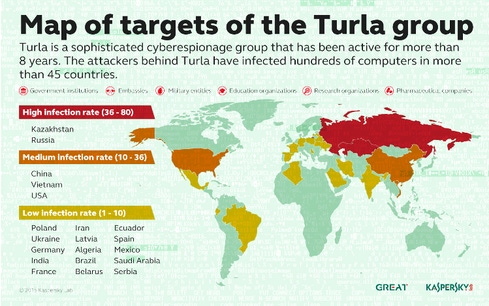
The so-called Turla group -- aka Snake -- hijacks unencrypted downstream satellite links from customers of satellite providers in the Middle East and Africa, and then uses those connections to exfiltrate data from its cyber espionage victims, researchers from Kaspersky Lab say. Turla is best known for targeting government agencies, embassies, military, pharmaceutical, and research organizations in the US, Kazakhstan, Russia, Vietnam, and China.
Unencrypted one-way satellite communications are widely known to be vulnerable to hacking. A researcher at Black Hat USA last month demonstrated how he was able to hack the Globalstar Simplex satellite data service using equipment he purchased for less than $1,000. Colby Moore, information security officer with Synack, says an attacker could intercept, spoof or interfere with satellite communications between tracking devices, satellites or ground stations because the Globalstar network doesn't encrypt those links nor digitally sign or authenticate the data packets. Globalstar maintains that "many … Globalstar devices have encryption" deployed by its integrators.
Kurt Baumgartner, principal security researcher at Kaspersky Lab, says his firm believes the Turla cyber espionage gang has been employing hijacked satellite links for about seven years now--almost as long as the group has been in action. "We've seen these IPs cycled" in Turla's activities, he says.
It's all about keeping their underlying command and control infrastructure operational and hidden from the prying eyes of researchers and others. But Turla isn't the only group that's employed satellite communications for their C&C, Baumgartner says. "We've seen a couple of other groups" as well, he says.
The notorious Hacking Team is among those that have used satellite-based IPs, as has the Xumuxu hacker group and the pro-Iranian Rocket Kitten hacking group.
"This is an unusual technique," Baumgartner says. "It's selectively used by them [Turla]. Almost everything Turla does has some sort of criteria selection … Turla is one of the stealthier actors who have put a lot of effort into maintaining and investing in infrastructure so they're really trying to maintain the anonymity of their infrastructure."
They're basically spoofing the legitimate satellite customer, who is none the wiser, he says. "The data they are stealing flows over the link paid by" the customer, he says. Turla doesn't bother hacking that customer's data--that's not its goal. "They wouldn't be able to do [this hijacking] if the link was encrypted," Baumgartner notes.
The technique works like this: Turla "listens" via an inexpensive antenna-based system for downstream communications from a satellite provider to spot active IP addresses of users online and then hijacks that connection. The pilfered satellite link is then used to siphon stolen information from "high profile" targets of Turla, according to Kaspersky's research.
"The data travels through conventional lines to the satellite Internet provider's teleports, then up to the satellite, and finally down from the satellite to the users with the chosen IPs," Kaspersky says in its new Turla research, published today.
Kaspersky Lab stops short of calling out Turla as a Russian nation-state group: it describes Turla as a "Russian-speaking" cyberspying operation. But other security firms, including Recorded Future, believe it's a Russian-based hacking operation.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024


