Say hello to the privacy revolution where an emerging backlash is being spurred by NSA spying, mass data collection and plain old common sense.
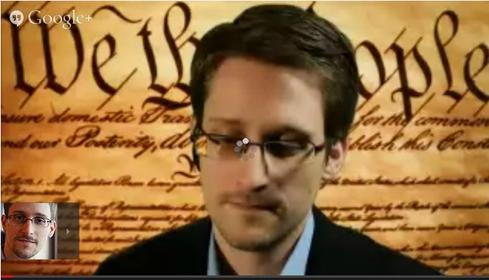
March Madness is a term typically reserved for men’s college basketball. This March however, news headlines from NSA whistleblower Edward Snowden and a 60 Minutes TV expose on the issue of privacy in America have added to the madness in a different and more frightening way.
"The NSA is setting fire to the future of the Internet,” Snowden declared during a live chat at the South by Southwest Interactive Festival on March 10th. Speaking directly to the American people for the first time since fleeing the country in June of 2013, Snowden took the opportunity to reiterate his strongly held belief that our federal government has burned the parchment on which our fourth amendment rights of freedom and democracy were transcribed by our forefathers centuries ago.
In Snowden’s world view, the NSA’s actions are ironic because by employing mass surveillance on everyone, the NSA minimizes its own resources to counteract the terrorism it wants to subdue. Snowden cited two White House studies that concluded there were no benefits gained by collecting such big data and that such action actually impeded the effectiveness of law enforcement to protect us from real threats.
Regardless of your take on Snowden, his saga is just a small chapter in a larger story. The night before Snowden’s appearance, the CBS news show 60 Minutes aired a riveting and frightening expose’ on data brokers -- organizations that collect, analyze, and sell our personal information as a commodity. We’re not just talking emails and contact lists; we’re talking our medications, habits, and daily activities.
Lest you think data brokering exists as a fringe industry made up of a few derelicts and frustrated former hackers, the truth is data brokering is a huge industry consisting of thousands of companies buying and selling our privacy to advertisers, the government, and other brokers.
The government doesn’t drive this industry as much as willingly participate within it. The real guilty parties are the researchers, advertisers, and Internet companies who encourage such behavior -- if not state their financial revenue model entirely upon it. Truth be told, the data brokers have hit a gold mine with the Internet. 60 Minutes for example, pointed out how the largest data broker has collected on average 1,500 tidbits of information on more than 200 million Americans. These are not suspected terrorists, but rather everyday citizens having their online diaries sold underneath them without their knowledge or approval.
As this situation comes to light even further, we must ask ourselves two questions: are we okay having our online activities and content mined and -- more important -- what can we do about it? Snowden and others argue that the best weapon would be a new world Internet order in which "end-to-end encryption" solutions make the means employed by the NSA and others impossible. Such a solution sounds great on paper, but there are two significant roadblocks:
1. It is nearly impossible to create such encryption in an easy-to-use format for geographically dispersed people using real-time communication services such as chat or even document sharing.
2. Companies such as Google, Facebook and others are unlikely to adopt this type of encryption because it would destroy their advertising platforms -- not to mention their advertising philosophy where its members are products and the advertisers are customers.
That said, the technology community, as Snowden sees it, should accelerate development of new encryption solutions, and without the NSA's guiding hand on standards. In the end, he exhorted attendees at SXSW to become 'firefighters' who will extinguish the flames of the burning Internet by choosing service providers that have respect for users’ privacy and don't aggregate a packet of data to hand over to the government—regardless of whether the government knocks and asks for the data or comes uninvited through the proverbial back door.
The digital privacy revolution is here, it’s happening and we all need to be a part of it. Use private search engines such as DuckDuckGo, access the web with privacy-centric browsers such as FireFox, choose next-generation social media companies that don't spy on or track their members, and follow Canada Information and Privacy Commissioner Ann Cavoukian‘s "Privacy By Design" development model that embeds privacy and data protection throughout the entire lifecycle of a technology -- from early design stage to deployment, use and disposal.
What we gain through innovative technology that advances our ability to communicate should be enjoyed without the watchful eye of a Big Brother, data brokers, or strangers lurking in the background. Privacy is a natural born right and not a luxury item. Some people call this emerging privacy backlash the privacy revolution. To me it’s common sense.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




