Annual Cisco privacy study also reports that 90% of organizations say their customers won't buy from them if they are not clear about data policy practices.
New research from Cisco found that most organizations over the past year turned to their privacy teams to help navigate and guide their shift to remote work in response to the COVID-19 pandemic.
"What we found was that roughly two years ago most companies barely had a privacy team; it was tucked away in a legal office," says Robert Waitman, director of data privacy at Cisco. "But with the shift to remote work because of the pandemic, privacy has become more important, mainly because employees were uncomfortable with the privacy of the tools available and the need for companies to provide a safe workplace."
The Cisco 2021 Data Privacy Benchmark Study, released ahead of Data Privacy Day on Jan. 28, found that privacy budgets doubled in 2020 to an average of $2.4 million. Overall return on investment was down slightly compared to 2019, but remained healthy with 35% of organizations reporting benefits at least two times their investments.
Here's a snapshot of the ROI companies reaped from privacy investment:
Built customer trust (76%): Respondents say customers better understand what's happening with their data and what the process is in the event of a breach;
Mitigated security losses (74%): Organizations spent less time and money responding to a breach.
Achieved operational efficiencies (74%): Data privacy controls resulted in more efficient operations.
Reduced sales delays (68%): Customers now spend less time trying to figure out their privacy policies, which resulted in shorter and more efficient sales cycles.
"We found at Cisco that customers took up a lot of our time asking about how their data was used, which would slow down the sales cycle," Waitman says. "We found that clear privacy policies streamline the sales cycle and also create transparency with the customers."
Stacy Scott, managing director in Kroll's Cyber Risk practice, says that companies were caught off-guard by the pandemic and had some business-critical questions to grapple with around data privacy, so it makes sense that companies leaned on their corporate privacy teams.
"This generation has never been through a pandemic, so there were a lot of questions to ask, such as: What type of privacy program we should set up? How do we keep employee data safe? And do we need to have monthly drive-bys at the homes of employees to pick up sensitive documents?" Scott says.
The rapid shift to more ecommerce also raised the privacy team's profile.
"Individuals are doing more with ecommerce and companies are interacting more with their customers online and also doing more online trade shows and conferences," Scott says. "All of this raised questions on how companies were going to keep all those communications and data private. And as people shifted their activities, the bad threat actors followed, which also put pressure on remote access systems and essential services, increasing privacy concerns."
Consumer-Driven Privacy Movement
Consumers have also played a large role in the move by companies to take privacy seriously. According to the Cisco benchmark report, a top concern of individuals over the past few years has been the lack of transparency when it comes to what data gets being collected and how it's used. Businesses and governments have not always been so clear on this front, and even when they strive for transparency, the complexity of the analytics, algorithms, insights, and inferences are often too complex for the general public to understand.
Waitman says many consumers have taken matters into their own hands: nearly one-third already have stopped buying from a company over their data policies or practices. Companies are increasingly recognizing this challenge, and 90% of organizations in this year's benchmark survey say that their customers will not buy from them if they are not clear about data practices and protection.
Privacy legislation has also played an important role in offering assurances that governments and organizations are being held accountable for how they manage their data. More than 130 countries now have omnibus privacy legislation and the vast majority of them have been passed in the past few years. Among respondents to the benchmark survey, 79% say privacy regulations have had a positive impact, 16% were neutral, and only 5% said that privacy laws have a negative impact.
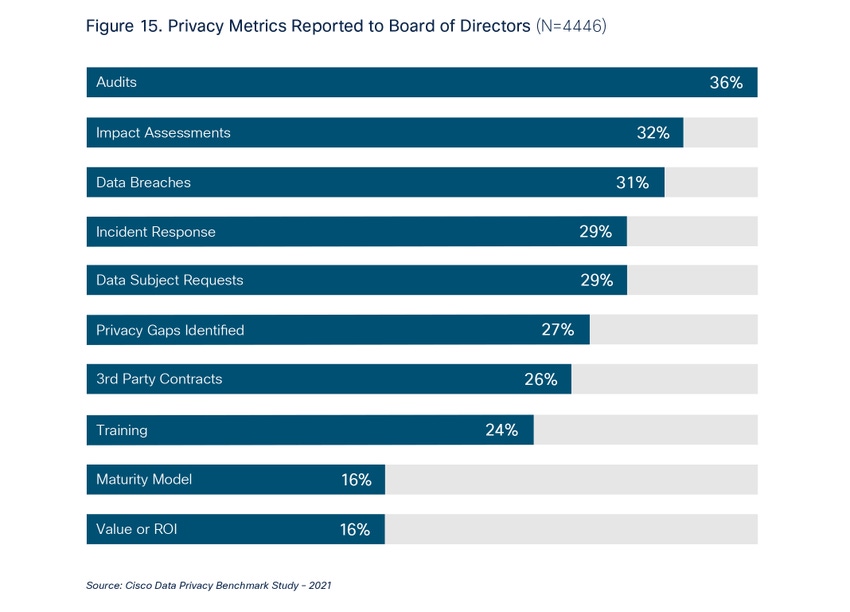
Another sign from the benchmark survey that privacy’s profile has risen: 93% of organizations now report at least one privacy metric to the board, with 14% reporting five or more privacy metrics. Among the most reported metrics are privacy program audit findings (36%), privacy impact assessments (32%), and data breaches (31%).
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




