A newly discovered strain of Locky ransomware has been discovered masquerading as legitimate Microsoft Word documents.
Another evolution of Locky ransomware is spreading through malicious attachments disguised as legitimate documents from productivity applications like Microsoft Word and Libre Office.
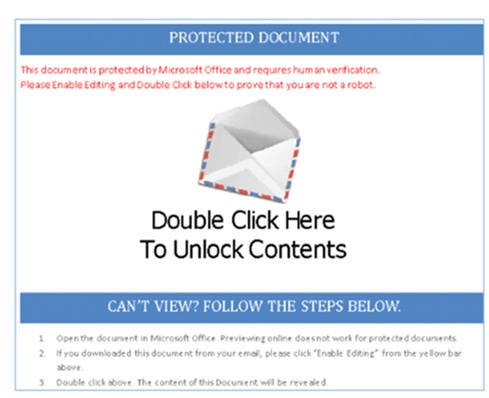
Researchers at Avira Virus Lab detected the ransomware earlier this week. This form of Locky has the same ".asasin" extension as a strain PhishMe picked up in October. However, it's crafted to manipulate users with a reportedly "protected document" disguised as this:
Users who double-click the image prompt a series of actions, which ultimately result in their files being encrypted under the ".asasin" file extension name. Multiple other files, with payment details, are written onto the disk.
Behind the image from the Word document, researchers saw a LNK file, otherwise known as a Windows shortcut. They realized the shortcut is intended to run a PowerShell script, which downloads another PowerShell script from an embedded link and runs it.
The second script connects to the Internet and downloads a Windows executable file, which includes several stages of code obfuscation and misleading data to trick victims and analysts into thinking the file is clean and from a legitimate Microsoft application.
Once it's on the victim's machine, the malware collects information about the operating system and sends it, encrypted, to the command-and-control server and retrieves the encryption key.
"We are seeing a rapid evolution in the way Locky is delivered," says Brendan Griffin, threat intelligence manager and malware analyst at PhishMe. "Locky stays the same, but the delivery techniques is where we've really seen the most change."
Evolution of Locky: What does it mean?
Ransomware is a growing problem for many organizations, and Locky is a common attack to watch.
"Locky has been one of the most popular malware libraries for a long time," says John Pironti, president of IP Architects. "It has been maturing, and that doesn't surprise me because it has been successful in financial gain."
It's common to see adversaries refresh and renew old approaches to see which is most effective, he continues. Attackers will slightly change their links or scripting to initiate activities to get to the same payload. The idea is to avoid detection and trick more users.
It's "misleading" to call this recent finding a new strain of Locky, Griffin adds. The ".asasin" strain, which PhishMe also detected, is a more robust and more verbose script application delivery than other forms of Locky seen in the past. It collects basic information off the machine; nothing personally identifiable. This is the same malware arriving on a different path.
"We've seen people embed scripts inside of Word documents, Excel links, things like that as a way to generate code and scripts that can grab more malware packages," Pironti says. People are more likely to open an attachment, the vector in Avira's finding, than they are to click a link.
"We spend so much time telling people not to click links … and not nearly as much time telling them not to click attachments," Pironti adds. Many employees click attachments all day as part of their jobs; to them, Word or Excel files aren't as suspicious as a potentially phishy link.
He notes that the ".asasin" extension is amusing. "They want to work off fear and force people to pay," he says.
This evolution also underscores how attackers often revert to simple techniques, Griffin adds. They're taking advantage of the fact that phishing emails, while basic, work. "Why would they choose a really complex, sophisticated, unreliable means of delivering malware?" he says.
Defending against fake applications
Griffiin points out that this is a clear example of abuse of Microsoft's Dynamic Data Exchange (DDE), a protocol on which Microsoft just published guidance for users.
Earlier this week, Microsoft published an advisory, following activity by Fancy Bear, which abused DDE fields to distribute malware. Microsoft is not planning to issue a patch but has provided steps for administrators to disable DDE, a protocol for transferring data between applications. If exploited, an attacker could assume control of an affected system.
Admins can turn off DDE by creating and setting registry entries for Microsoft Office based on the applications installed on the system. After this, data will no longer update automatically between applications, which could be problematic for people who rely on data feeds to update Excel. Microsoft warns doing this incorrectly could cause serious problems that would require reinstallation of the operating system.
Related Content:

Join Dark Reading LIVE for two days of practical cyber defense discussions. Learn from the industry’s most knowledgeable IT security experts. Check out the INsecurity agenda here.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




