Some recent stats on adoption rates and perceptions about risks surrounding the Internet of Things.
May 19, 2016
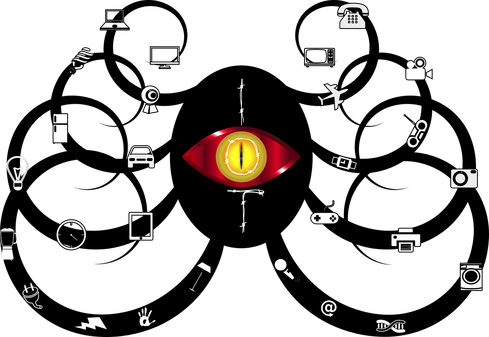
With wearable devices, smart building components and other embedded devices exploding into the enterprise network, the Internet of Things (IoT) is a hot-button topic for many security folks. The hockey stick growth of IoT devices and sensors will require teams to adjust their strategies and Gartner predicts that by 2020, IoT security will make up 20 percent of annual security budgets. Here are a few statistics about the risks posed by IoT growth.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




