Enterprises may not notice a huge impact on their network's bandwidth, but other repercussions may loom in the background.
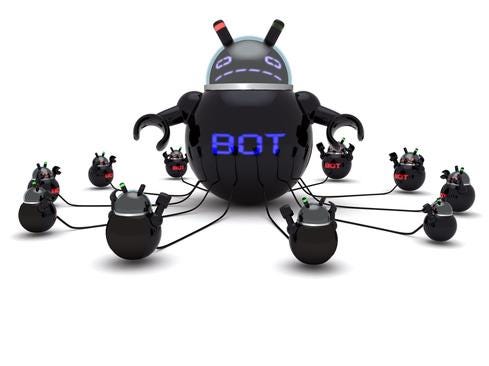
The WireX Android botnet last month snagged tens of thousands of mobile users, in order to wage DDoS attacks against organizations in multiple industries.
While it's clearly taxing to be on the receiving side of a DDoS attack, enterprises that find their mobile devices commandeered as bots also have reason for concern.
"Enterprises may notice their upstream traffic flow will be slightly constrained, but the impact will be negligible," says Robbie Forkish, Appthority CTO. However, Forkish and other security experts note it's still worth a company's time and effort to prevent their mobile devices from becoming bots.
For example, companies may find their IP addresses blacklisted if their mobile devices are swept up into a botnet, notes Andrew Blaich, a security researcher at Lookout.
James Plouffe, lead solutions architect with MobileIron, agrees.
"If you are an enterprise and part of a botnet, then you're consuming bandwidth for things not related to your company," Plouffe says. "Also, it could appear your company is the source of the attack and it could be bad for your company's reputation and you may incur some liability."
In addition to these issues, a company may find that once its mobile workforce is infected with malware, the attackers could turn the bots into another malicious purpose.
"The attacker could change the instructions and have it infiltrate confidential information on the device," says Robert Hamilton, director of product marketing at Imperva.
Here are 10 steps IT security teams can take to reduce the odds their mobile devices will get recruited as bots:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




