
Cybersecurity In-Depth: Digging into data about the latest attacks, threats, and trends using charts and tables.
Threat is spreading widely via spam campaigns, infecting systems with a new malware loader.
SquirrelWaffle is a new malware loader that infects systems using malicious documents delivered via a link in an email message. Threat actors use the malware loader to establish an initial foothold onto systems and their network environments. The adversaries can either download additional types of malware or further compromise the network, depending on how they choose to monetize the attack. In many cases, SquirrelWaffle is being used to deliver and infect systems with Qakbot and the penetration-testing tool Cobalt Strike.
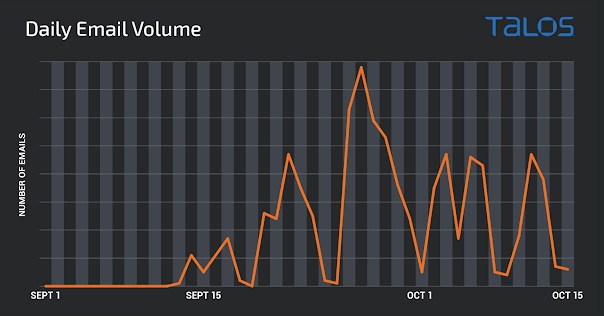
Beginning in mid-September, Cisco Talos observed malspam campaigns delivering malicious Microsoft Office documents designed to infect systems with SquirrelWaffle. The messages typically contain hyperlinks to malicious ZIP archives hosted on attacker-controlled Web servers. The chart, above, illustrates the volumetric trajectory of these campaigns between Sept. 1 and Oct. 15, 2021. Due to the prevalence of these campaigns, organizations should be aware of how SquirrelWaffle could be used to further compromise corporate networks.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024

