
Cybersecurity In-Depth: Digging into data about the latest attacks, threats, and trends using charts and tables.
It's not hacking if organizations fail to terminate password access after employees leave.
An alarming number of organizations are not properly offboarding employees when they leave, especially in regard to passwords. In a March PasswordManager.com survey of 1,000 U.S. workers who had access to company passwords at their previous jobs, 47% admitted to using them after leaving the company.
Security teams should be terminating access to all employee accounts, such as email, cloud applications, and internal tools, after employees leave. For accounts or services where multiple employees share passwords, those passwords should be rotated to ensure that the former employees no longer have access.
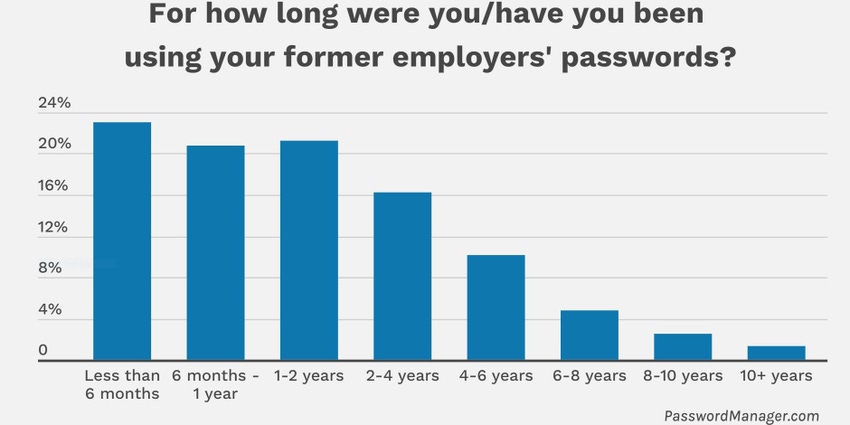
According to the survey, 58% of respondents indicated they were still able to use their former company's passwords after they left. One in three respondents said they had been using the passwords for upwards of two years, which is a distressingly long time for organizations not to be aware of who is accessing those accounts and services.
“Ideally the company creates standard operating procedures or consistent schedules of updating passwords based on criticality,” says Daniel Farber Huang, head of privacy and cybersecurity at PasswordManager.com.
When asked what they use the passwords for, 64% said to access their former email accounts and 44% to access company data. Though the majority of the respondents, 56%, said they were accessing the accounts for personal use, a concerning 10% said they were trying to disrupt company activities.
A survey from Beyond Identity in 2022 had similar findings: Fifty-three percent of employee respondents admitted to using their access to harm their former employers, and 74% of business leaders reported suffering damages from former employees who exploited their digital access.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024

