The beta release of Google Cloud SCC will include broader coverage across the cloud platform and more granular access controls, among other features.
Google today released its Cloud Security Command Center (Cloud SCC) in beta mode to Google Cloud Platform (GCP) users.
Cloud SCC was first announced and deployed in alpha mode back in March. Google's idea behind the tool was to give admins a single platform to view assets, vulnerabilities, and threats across the organization. Now, as part of the beta release, the team is adding new features.
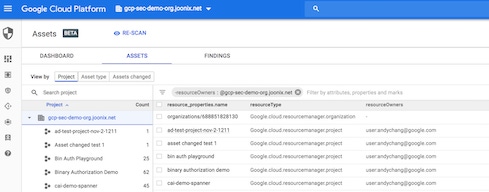
For those who haven't tried it, Cloud SCC takes inventory of cloud assets, alerts to unwanted changes in those assets, and detects risky areas throughout the environment. Its findings are collected in a dashboard and data platform so admins have a clear look at their cloud security.
The beta release comes with coverage across a broader range of services: Cloud Datastore, Cloud DNS, Cloud Load Balancing, Cloud Spanner, Container Registry, Kubernetes Engine, and Virtual Private Cloud. Google has also added 13 identity and access management roles for more granular access control across Cloud SCC, and expanded client libraries like Java, Node, and Go.
Cloud SCC now also includes additional examples of how to create notifications when changes occur or trigger Cloud Functions from a Cloud SCC query, Google officials explain in a blog post on the news. Admins can view and search for new and deleted assets over a specific time period, better manage asset discovery, and self-serve onboarding with the GCP Marketplace.
GCP admins can use the beta release of Cloud SCC to evaluate security risks and vulnerabilities – for example, which cloud storage buckets are publicly accessible, which virtual machines have public addresses, and which firewall rules should have tighter permissions. Admins can also see whether users outside of their designated domain can access corporate resources, they note.
Asset inventory lets admins view resources for their entire GCP organization or limit their scope to specific projects and view new, deleted, and total assets for a particular time frame.
As part of this update, Cloud SCC integrates with Google's cloud security services (Data Loss Prevention API, Forseti, Cloud Security Scanner, and Google anomaly detection). It also connects with third-party cloud tools from Cavirin, Chef, and Redlock.
Related Content
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




