The tool is designed to help identify misconfigurations and compliance violations in the Google Cloud Platform.
Google Cloud today released the beta version of its new Security Health Analytics service for helping detect and act on misconfigurations and compliance violations across Google Cloud Platform resources.
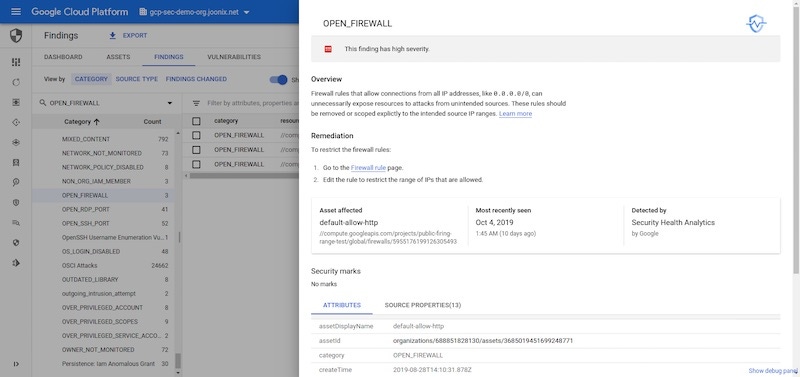
Security Health Analytics integrates into the Cloud Security Command Center (Cloud SCC). A dashboard shows potential security issues, or "findings," which when clicked display a step-by-step plan for how to remediate the problem. An admin might be alerted to an open firewall or overly privileged access to a storage bucket, along with a direct link to the affected resource.
The tool now supports Center for Internet Security (CIS) benchmarks, Google says, and is fully certified by CIS to monitor GCP Foundation benchmarks. These are recommendations for maintaining security and compliance across GCP resources. Security Health Analytics will monitor for assets that violate CIS recommendation 5.1, for example, which relates to the identification and remediation of storage buckets that are left accessible to the public.
{image 1}
Security Health Analytics shows steps to remediate an open firewall.
GCP customers can enable Security Health Analytics from Security Sources in Cloud SCC.
 Check out The Edge, Dark Reading's new section for features, threat data, and in-depth perspectives. Today's top story: "14 Hot Cybersecurity Certifications Right Now."
Check out The Edge, Dark Reading's new section for features, threat data, and in-depth perspectives. Today's top story: "14 Hot Cybersecurity Certifications Right Now."
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




