The malware campaign uses the Sugarsync cloud storage app to distribute malware that steals user credentials and monitors online banking activity.
Netskope Threat Research Labs today published a report digging into the CloudFanta malware campaign, which is suspected to have stolen more than 26,000 email credentials since it began operation in July 2016.
CloudFanta leverages the Sugarsync cloud storage app to distribute malware capable of stealing user credentials and observing online banking activity to obtain users' information.
Users are primarily targeted by CloudFanta through an attachment or link, which appear in a spearphishing email. When victims click the link or execute a file, it prompts the delivery of a JAR file, which acts as a downloader for Dynamic Linked Library (DLL) files on the back-end.
These files are used to steal victims' email credentials, send malicious emails on their behalf, and monitor their online banking activity.
The CloudFanta malware is stored on Sugarsync, which the attack uses for hosting drive-by-download files. CloudFanta goes undetected by traditional, network-based security solutions because it delivers DLL files with the ".png" extension and uses SSL/HTTPS communication.
"This malware campaign is looking for the users' email addresses and passwords," explains Ravi Balupari, director of engineering and cloud security research at Netskope. "It's also targeting specific users," he says, noting CloudFanta is primarily affecting users in Brazil.
How does it work? If a victim enters their email credentials from an infected machine, their login page will be redirected to a phished login page so their information can be stolen. Victims' data is uploaded to the C&C server, and they are redirected to their original email login page.
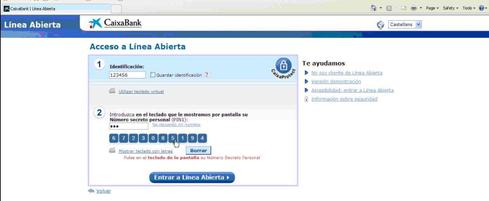
CloudFanta also bypasses sophisticated security measures on banking websites to steal victims' credentials. Many banks require users to log in using virtual keyboards, Balupari explains.
When victims attempt to access their accounts, the malware captures a screenshot of the active window for each mouse click. It saves these in a text file containing the number of clicks, which can help attackers view victims' passwords.
Sugarsync wasn't the only software abused by CloudFanta; early versions of the malware used Dropbox to host malicious files. However, Sugarsync's broad user base and ability to automatically download links made it easier to spread malware.
The cloud provides a convenience to attackers who want broader access. Traditional malware hosts malicious files on other servers, but cloud-based malware makes it easier for hackers to access malware everywhere. "Typically, cloud-based apps provide a convenient method for downloading files," he explains.
What's more, he continues, many traditional business security measures don't provide mechanisms to protect the cloud. This allows hackers to use cloud-based software to target more users.
Netskope has partnered with Sugarsync to stop the spread of CloudFanta malware by taking down infected URLs. The two collaborate to provide users with information on malicious links, and monitor changes happening in CloudFanta and other malware campaigns.
"We'll definitely see a rise in cloud malware campaigns going forward," says Balupari. "Enterprises and customers who have been adopting cloud apps need to add additional layers of security."
There are several steps businesses can take to prevent the spread of cloud malware; for example, implementing two-factor authentication and protection to prevent data leakage.
IT pros should also detect and track unsanctioned cloud services and enforce data loss prevention policies to manage the data entering and leaving the organization. They should also back up critical content stored in the cloud.
Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




