Shadow IT is a growing risk concern among IT pros, with most reporting users have gone behind their backs to set up unapproved cloud services.
A conflict of interest is driving the rise of shadow IT among organizations.
Tech pros are responsible for controlling and safeguarding data; employees want to accomplish tasks as efficiently as possible. As a result, more workers have begun to use cloud-based tools without consulting IT to verify their security.
This is the key takeaway from a new SpiceWorks study entitled "Data Snapshot: Security, privacy, and the shadowy risks of bypassing IT." To learn more about the growth and risk of this practice known as "shadow IT," researchers surveyed 338 IT pros across North America, Europe, the Middle East, and Africa.
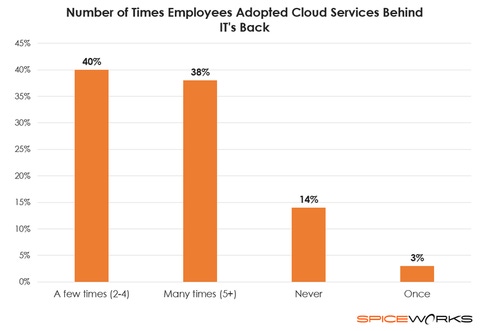
Results indicate shadow IT poses a growing risk to businesses. Eighty percent of IT pros report their end users have secretly set up unapproved cloud services, and 40% claim users have gone behind their backs at least five times.
To employees, it may not seem dangerous to adopt cloud services like Dropbox or Google, which they often use outside the office, but tech pros are concerned. Nearly 40% of respondents believe shadow IT has increased their data's vulnerability in the past five years.
"End users don't typically understand the subtleties of end-to-end encryption, multi-factor authentication, or user access controls," explains Peter Tsai, IT analyst at SpiceWorks. "As a result, they might share confidential data using unapproved IT services where they might accidentally be made public or pass through insecure, unencrypted channels through which a hacker could intercept them."
Which services are driving the threat? Cloud storage services top the list, with 35% of IT pros claiming these are most vulnerable to attack. Next up are Web-based email services like Gmail and Exchange Online, which are considered most vulnerable among 27% of tech pros.
"Because it only takes a few minutes for anyone to sign up for these accounts, it becomes trivial for even non-technical users to set up," explains Tsai. "However, most end users don't think through the security implications of sending or storing sensitive company data using free services that arean't necessarily designed with enterprise security in mind."
It seems the risk is greater for larger companies. Nearly half (47%) of IT pros at companies with 500+ employees report their data is at greater risk. As businesses grow, it's harder for IT managers to keep track of employees and the multitude of cloud services they use.
The threat is certainly growing, but what are businesses doing to mitigate risk? Most (72%) claim their company sufficiently invests in protecting their data, and 68% say data privacy is a top priority.
When it comes to best practices for keeping data safe in the cloud, respondents were nearly equal on the importance of three security measures: end-to-end data encryption (68%), multi-factor authentication (67%), and user access controls (67%). More than half (51%) of IT pros said vetting a cloud vendor's security practices is essential.
Tsai also emphasizes the importance of ensuring employees understand how unapproved cloud services could put corporate data at risk. IT pros can also restrict the websites end users visit and the software they install.
"Additionally, IT departments should strive to understand user needs and provide the tools and applications they want to use, so workers aren’t tempted to go behind IT's back to begin with," he adds.
The study indicates there is more that could be done to improve security. Less than half (47%) of respondents say their company conducts regular security audits. Less than one-third (28%) are actively trying to improve their data privacy strategy following highly publicized breaches.
Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




