The first in a series of articles shining a spotlight on women who are quietly changing the game in cybersecurity.
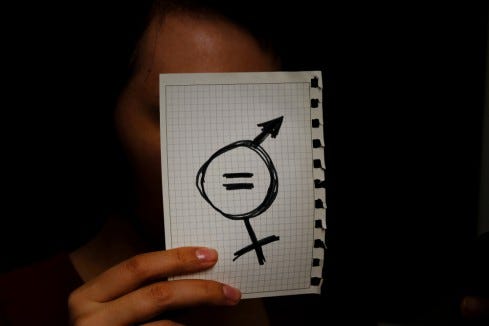
Image Source: Elvira Koneva via Shutterstock
Kelly Jackson Higgins contributed to this article.
Cybersecurity doesn't have enough people.
The industry is expected to have 1.8 million unfilled positions by 2020, a 20% increase from 2015 and signs of a skill shortage continue to plague the industry. Businesses don't have enough security professionals in-house, and many lack the necessary skillsets.
Gender inequality pervades the male-dominated tech space, meanwhile, where only 49% of female employees feel both genders are treated equally, according to a new report from Indeed. The lack of diversity extends into cybersecurity, where women make up only 11% of the workforce, reports (ISC)². There is no clear-cut answer for the massive gender gap, but a number of factors seem to be at play. Consider salary, for instance: women earn lower salaries than their male counterparts in cybersecurity and women who identify as minorities make even less.
In an effort to celebrate and shine a light on some of the work women are doing in cybersecurity, Dark Reading is publishing a series of articles that identify women who may not be as well-known in the industry (yet), but who are making key contributions. This first installment includes ten women in various sectors of cybersecurity, who were selected based on recommendations and research. The list is in no particular order.
This is just the first in a series on women you may not know about, but whose work you might see more of in the future. If you know someone who fits the bill, please send us their names and any information about them and their work, to [email protected]. We expect to see the list get much longer.
Read more about:
Black Hat NewsAbout the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




