Modern cybersecurity today is all about risk management. That means eliminating and mitigating risks where possible, and knowingly accepting those that remain.
October 20, 2016
Organizations around the world are implementing mobility, cloud computing, the Internet of Things (IoT), business intelligence, and social media technologies at breakneck speeds in order to remain competitive and relevant in today’s digital economy. However, with the rapid implementation of these technologies, new weak spots are emerging for attackers to exploit. And those adversaries are becoming progressively more sophisticated, launching threats that are increasingly pervasive and harder to detect.
The challenge with many digitally disruptive technologies is that security is often an afterthought. Couple this with the fact that we’re seeing these devices often being connected to infrastructure that is not up to today’s cybersecurity demands, and we have a significant problem on our hands.
Businesses that want to add emerging technologies such as IoT to their networks need to regularly assess their cyber hygiene and the resilience of their existing infrastructure. It’s clear that hackers are well aware of how prevalent unpatched and outdated solutions are within organizations and how these aging technologies leave them vulnerable.
Take, for example, the string of ransomware attacks earlier this year. Hackers exploited vulnerabilities within Jboss servers that were identified five years ago to aid in delivering ransomware attacks. From this vulnerability alone, approximately 3.2 million machines were at risk of infection, and more than 2,100 compromised systems were already present at the time of the investigation.
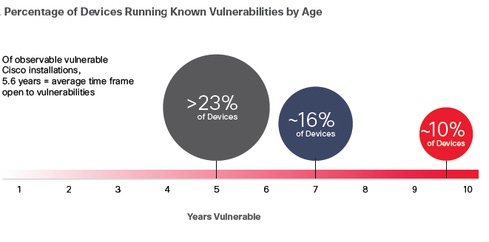
In its 2016 Midyear Cybersecurity Report, Cisco found that more than more than 90% of devices across customer environments had known vulnerabilities in the software they were running. Additionally, the company found that almost all of its sampled routers and switches on the Internet — had, on average, 28 known vulnerabilities. The devices had been running known vulnerabilities for an average of 5.6 years. More than 23% of these devices had vulnerabilities dating back to 2011, nearly 16% had vulnerabilities that were first discovered in 2009, and almost 10% had known vulnerabilities older than 10 years.
Despite a growing awareness of the threats that target them, some organizations still aren’t practicing some of the fundamental steps of cybersecurity to ensure the level of resiliency needed to endure current threats. It is imperative for organizations to prioritize addressing the problem of aging infrastructure and systems. This isn’t just about patching old vulnerabilities that have been left to fester, but also assessing the overall strength and resilience of the deployed infrastructure and systems. The time has come for organizations to realize that they must move away from products that are no longer supported and can’t be upgraded to meet today’s security challenges.
Modern cybersecurity is about risk management — that is, eliminating and mitigating risks where possible, and knowingly accepting those that remain. Poor cyber hygiene — not patching, keeping outdated solutions in place, etc. — puts the overall resilience of an organization into jeopardy.
What Can You Do Today to Reduce Cyber Risks?
1. Reduce attackers’ time to operate: Attackers’ campaigns often take advantage of known vulnerabilities and can remain active and undetected by their victims for days, weeks or longer. Know what is in your network and deploy the basics — patching, password management, and segmentation — to impede lateral movement and propagation.
2. Improve your network hygiene: Upgrade aging infrastructure and systems, patch quickly, and consistently back up your data.
3. Conduct a risk-focused evaluation of the existing hardware and software: Rank products in terms of which ones create the most effective, essential value, and determine how much risk each product brings on based on its age, vulnerabilities, and cyber resilience. With this, organizations can develop a prioritized list for updated technology investments with resilience built in.
In the end, it’s not enough just to patch old vulnerabilities or buy the latest security solution to address a specific threat. Organizations have to assess the overall strength and resilience of their infrastructure and systems to face fast-moving and aggressive threats. It’s time to move away from products that are no longer supported and can’t meet today’s cybersecurity challenges, and time to embrace a risk-based approach to cybersecurity.
Related Content:
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




