Users regularly reuse logins and passwords, and data thieves are leveraging that reality to breach multiple accounts.
By now, we have all received at least one email disclosing to us that the personal information we provided to an organization was leaked or stolen. It could have been a social media platform, a bank, or a fast-food chain (Drizly, an alcohol delivery service, was one of the latest to announce a breach). Seemingly no industry has been exempt from data breaches, inadvertent leaks, or misconfigurations by the governing body to date.
Since LinkedIn's notable 2012 breach affecting 170 million users, we have seen many other significant security incidents exposing massive amounts of user data. Sometimes it's billions of accounts — billions! For example, in 2019, researcher Bob Diachenko discovered an unsecured Elasticsearch server that leaked records related to 1.2 billion people.
Considering the amount of publicity these incidents receive, does the data from well-known mega-breaches have any value within the underground economy, and do end users continue to be affected today? Many people may be surprised by the answer.
In most scenarios, organizations follow guidelines of responsible disclosure in the event of a data breach or cybersecurity incident. This may look like offering complimentary breach remediation, perhaps by third-party remediation or credit-monitoring services such as Tri-Credit bureau organizations. This is typically followed up with recommendations for end users to change the credentials affected. And then the organization itself resets, locks, or removes the impacted leaked data rendering it unusable, and end users reset their own passwords … right?
Data from Highly Publicized Breaches Are Valuable Today
Remember these?
2014: Yahoo (3 billion)
2017: Equifax (163 million)
2018: Under Armour (150 million), Panera Bread (37 million)
2019: Verifications.io (200 million), Canva (140 million), Zynga (173 million)
A majority of this leaked data, and more, continues to be readily available for little to no cost, found within commodity-based threat actor forums or open source intelligence environments, or recycled in forums and sold as smaller unique datasets, pivoting off the original leaked datasets, and leveraging the users' password reuse on other third-party accounts.
For example, researchers at Vigilante obtained 100 Citibank user accounts — completely valid credentials — belonging to valid Citibank customers. These credentials are directly from well-known breaches not related to a Citibank breach. In other words, threat actors took data from well-known, highly commoditized leaks and targeted other possible accounts those users might have, such as Citibank, by testing the credentials for a match.
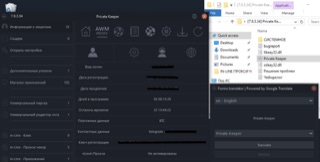
This is easily accomplished via well-known and easy-to-obtain cybercrime tools such as Private Keeper. This tool is touted as requiring no knowledge of programming skills and uses a simple and intuitive graphical user interface, highly capable of brute-forcing credentials. With such ease of use and lowered technological sophistication, this certainly broadens the threat-actor population who are willing to engage in cybercrime activity in order to turn a buck — most certainly endangering all online brands.
The Elephant in the Room
Today, there may be a lack of collaboration between organizations that represent midsize to large ecosystems of users, for example. That is to say, it does not appear that third-party organizations unrelated to a mega-breach are monitoring for leaks, cross-comparing their user base, or identifying their own users of the mega-breach and forcing password resets of their own user, considering the high probability of password reuse.
When mega-leaks occur, many other ecosystems become endangered due to the tendency of users to reuse the same credentials on other sites. Not only well-known brands but even small to midsize organizations with an online presence should consider the issue of password reuse stemming from previous mega-leaks as a primary threat vector.
While I do believe organizations that are breached continue to monitor for attribution around the leak, and they work to remediate their own users to the best of their ability, other satellite organizations may not confirm if their end users have reused the credentials of their infrastructure.
How We Shift Away from Account Takeovers Due to Breaches
We know that threat actors tend to leverage the simplest threat vectors and unsophisticated password-reuse campaigns, which tend to be the most successful and profitable campaigns for cybercriminals. Despite this, most end users have stopped paying much attention to new data breaches. Individuals are not proactively working to protect their accounts in the easiest ways possible.
This means that when mega-breaches occur, the leak affects not only the breached organization but all other online ecosystems that share the same user base. And threat actors will continue to leverage massive data leaks to compromise user accounts at other online ecosystems, in addition to reselling it.
My vision for the future is that organizations with personal data should work as a collective. When a breach occurs at one organization, all organizations should be enforcing new credentials and rejecting known compromised credentials. This can help to curb account takeover, fraud, and misrepresentation. We have seen that account credentials from eight years ago are being reused today. Organizations should potentially consider evaluating well known breaches of correlations between their own ecosystem and well-known breaches, remediating matches, not only enforcing step-up authentication challenges in the login process but also enforce users of formerly known data leaks to leverage two-factor authentication.
Related Content:
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




