The key to managing partner security risk is having truly verifiable evidence.
In the legend of Troy, Greek warriors spent a significant amount of time trying to break into huge walls surrounding the city until Odysseus had a clever idea: leave a wooden Trojan horse outside and hide the soldiers inside. Today, the city of Troy is your company and the modern equivalent to the Trojan horse are your third party systems.
Organizations spend inordinate amounts of money protecting their fortresses, but they neglect the immediate risks posed by unfortunate partners. Today, organizations attempt to rein in third-party risk through on-site visits, security questionnaires, and intrusive, one-time audits. These security measures are an exercise in trust, but difficult to fully verify. As a result, forward-leaning organizations are looking for a fresh approach to manage their security-risk environment.
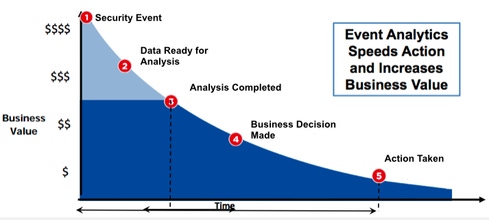
If you have hundreds of vendors today, there is almost no way to know all of the security-risk issues they have. You send a questionnaire, jump on the phone, incorporate legal provisions into the contract, and pray that vendor responses are correct. The key to managing partner risk is having truly verifiable evidence. In business, the faster you are able to make an informed decision the more business value you can extract.
You also need to know which vendors pose less risk to your company and deserve fast-tracked assessments. As facts about third-party security risk become more readily apparent, proactive management will be needed. How do you get there? You can start by following these seven steps:
Get your executive team to buy in and the general counsel to participate
Separate your vendors into groups of low, medium, and high criticality.
Ask for objective evidence, supporting answers that third parties presented in the questionnaire.
Work with, not against your partners.
Evaluate and measure vendor performance as a continuous process.
Establish regular touch points and personal relations with vendors to review common risk threats
Reserve the right to audit vendors.
Make the case with information
The independent security risk evidence that is now available via technologies that span big data, threat intelligence, and governance, risk, and compliance systems can help organizations make smarter decisions. When this information is accurately placed in a comparative business context, companies can begin to prioritize vendor management resources and speed up the time to remediation. With this intelligence, we can improve the maturity of our risk management and vendor management programs. But this intelligence must be in a business-friendly context.
The bottom line: technical metrics alone will not suffice. We need to stop pretending the paperwork we are pushing around is protecting our organizations and our customers. We need stronger levels of trust based on rapid, factual, and accurate information that is completely independent from our partner relationships.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




