Attackers leveraging the flaw are using infrastructure associated with other criminal groups, including ransomware-as-a-service operators, the company says.
September 16, 2021
Microsoft on Wednesday once again urged organizations to apply a security update it issued last week for a critical remote code execution (RCE) vulnerability in its MSHTML browser engine, citing growing attacker interest and exploit activity around the flaw.
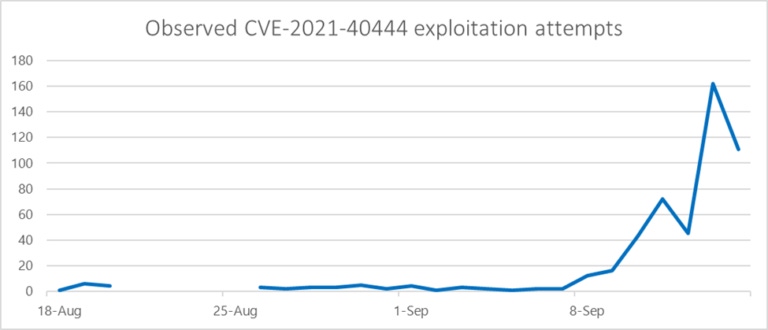
In an advisory, the company linked the increase to a third-party researcher's public disclosure of proof-of-concept (PoC) exploit code for the vulnerability (CVE-2021-40444), which was published on Sept. 8 and led to an almost immediate increase in exploitation attempts.
Since that disclosure, multiple threat actors have included the PoC into their attack kits, including ransomware-as-a-service (RaaS) operators, Microsoft said. Some of the infrastructure being used in attacks involving the vulnerability previously has been associated with malicious campaigns, including the delivery of Trickbot and BazarLoader backdoors.
RiskIQ identified the operator of the infrastructure as a RaaS syndicate called "Wizard Spider," which is also tracked by various other names, including "Ryuk," DEV-0193 by Microsoft, and UNC1878 by Mandiant.
RiskIQ described the link between CVE-2021-40444 and the Wizard Spider/Ryuk operation as troubling. "It suggests either that turnkey tools like zero-day exploits have found their way into the already robust ransomware-as-a-service ... ecosystem," RiskIQ said. "Or [it suggests] that the more operationally sophisticated groups engaged in traditional, government-backed espionage are using criminally controlled infrastructure to misdirect and impede attribution."
CVE-2021-40444 is a vulnerability in MSHTML, also known as Trident, that gives attackers a way to drop malware on a system via a malicious ActiveX control embedded in an Office document. A user that receives the Office document would need to open it to trigger the malicious code. In these instances, the vulnerability would allow an attacker to download content from an external source without triggering the usual "Protected Mode" control that Windows uses to protect against content from potentially untrusted sources.
In many of the attack attempts that have been observed so far, threat actors leveraged the flaw as an initial access vector to install a custom Cobalt Strike Beacon loader — a legitimate penetration testing tool that can be used to scan networks for vulnerabilities. Use of the tool by cybercriminals surged 161% between 2019 and 2020, and it remains a high-volume threat in 2021 as well, Proofpoint said in a report earlier this year.
Microsoft first disclosed the vulnerability and released mitigations and workarounds in an advisory on Sept. 7. It later issued a patch for CVE-2021-40444 on Sept. 14 as part of its scheduled monthly security update. A threat group that Microsoft has identified as DEV-0413 began attacking the flaw several weeks prior, in mid-August, making it a zero-day flaw when it was first discovered. "DEV" is Microsoft's nomenclature for an emerging threat group or activity cluster that it hasn’t observed before. Others such as Mandiant use the term "UNC" to track previously unknown threat groups.
According to Microsoft, the DEV-0413 group's attacks in August were highly targeted in nature and affected fewer than 10 organizations. In those attacks, the threat actors embedded the malicious ActiveX control in emails that appeared to pertain to legal agreements and contracts. The earliest attack, on Aug. 18, involved a phishing lure that purported to be a job opportunity for a mobile application developer. Multiple application development organizations were targeted in the campaign, which involved the use of legitimate file-sharing services to deliver the lure.
A chart that Microsoft released with its advisory Wednesday showed that hundreds of organizations have been targeted in attacks seeking to exploit CVE-2021-40444 — with almost all the activity happening after Sept. 8. The company advised organizations to install the update it released Sept. 14 and to implement a control for blocking all Office applications from creating "child processes" — processes created by other processes.
RiskIQ, meanwhile, said its analysis suggests that the threat actor behind the initial exploit and Cobalt Strike payload is part of the Wizard Spider/Ryuk group, which means it is likely motivated by financial gain via ransomware. Another possibility is that the threat actor is separate and either shares or has compromised Wizard Spider's infrastructure and is using it to carry out espionage or financially motivated attacks.
About the Author(s)
You May Also Like
Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




