The evolving tactics increase the threat of ransomware operators, but there are steps organizations can take to protect themselves.
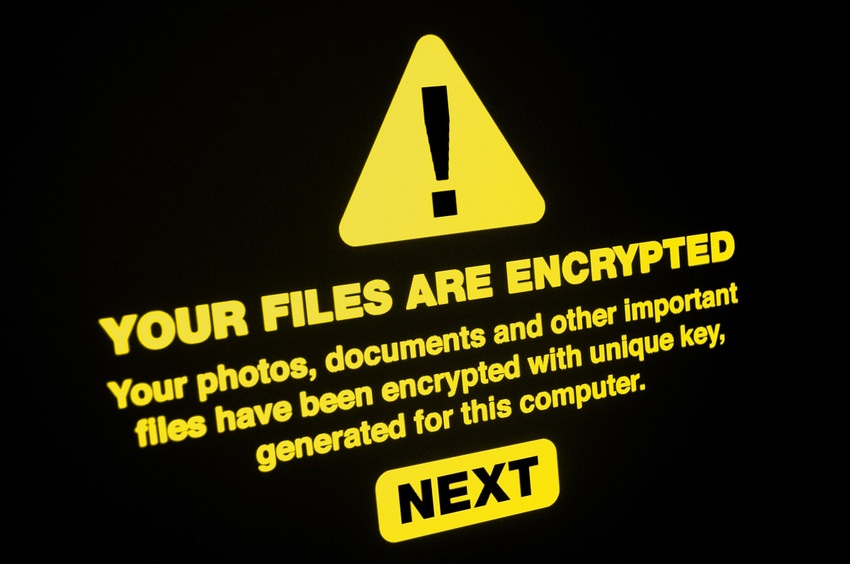
Cybercriminals are becoming more strategic and professional about ransomware. They increasingly are emulating how legitimate businesses operate, including leveraging a growing cybercrime-as-a-service supply chain.
This article describes four key ransomware trends and provides advice on how to avoid falling victim to these new attacks.
1. IABs on the Rise
Cybercrime is becoming more profitable, as evidenced by the growth of initial access brokers (IABs) that specialize in breaching companies, stealing credentials, and selling that access to other attackers. IABs are the first link in the cybercrime-as-a-service kill chain, a shadow economy of off-the-shelf services that any would-be criminal can purchase to construct sophisticated tool chains to execute almost any digital offense imaginable.
IABs' top customers are ransomware operators, who are willing to pay for access to ready-made victims while they focus their own efforts on extortion and improving their malware.
In 2021, there were more than 1,300 IAB listings on major cybercrime forums monitored by the KELA Cyber Intelligence Center, with nearly half coming from 10 IABs. In most cases, the price for access was between $1,000 and $10,000, with an average sale price of $4,600. Of all of the offerings available, VPN credentials and domain administrator access were among the most valuable.
2. Fileless Attacks Fly Under the Radar
Cybercriminals are taking a cue from advanced persistent threat (APT) and nation-state attackers by employing living-off-the-land (LotL) and fileless techniques to improve their chances of evading detection to successfully deploy ransomware.
These attacks leverage legitimate, publicly available software tools often found in a target's environment. For example, 91% of DarkSide ransomware attacks involved legitimate tools, with only 9% using malware, according to a report by Picus Security. Other attacks have been discovered that were 100% fileless.
This way, threat actors evade detection by avoiding "known bad" indicators, such as process names or file hashes. Application-allow lists, which permit the usage of trusted applications, also fail to restrict malicious users, especially for ubiquitous apps.
3. Ransomware Groups Targeting Low-Profile Targets
The high-profile Colonial Pipeline ransomware attack in May 2021 affected critical infrastructure so severely that it triggered an international and top government response.
Such headline-grabbing attacks prompt scrutiny and concerted efforts by law enforcement and defense agencies to act against ransomware operators, leading to the disruption of criminal operations, as well as arrests and prosecutions. Most criminals would rather keep their activities under the radar. Given the number of potential targets, operators can afford to be opportunistic while minimizing the risk to their own operations. Ransomware actors have become far more selective in their targeting of victims, enabled by the detailed and granular firmographics supplied by IABs.
4. Insiders Are Tempted With a Piece of the Pie
Ransomware operators also have discovered that they can enlist rogue employees to help them gain access. The conversion rate may be low, but the payoff can be worth the effort.
A survey by Hitachi ID taken between Dec. 7, 2021, and Jan. 4, 2022, found that 65% of respondents said their employees had been approached by threat actors to help provide initial access. Insiders who take the bait have different reasons for being willing to betray their companies, although dissatisfaction with their employer is the most common motivator.
Whatever the reason, the offers made by ransomware groups can be tempting. In the Hitachi ID survey, 57% of the employees contacted were offered less than $500,000, 28% were offered between $500,000 and $1 million, and 11% were offered more than $1 million.
Practical Steps to Improving Protection
The evolving tactics discussed here increase the threat of ransomware operators, but there are steps organizations can take to protect themselves:
Follow zero-trust best practices, such as multifactor authentication (MFA) and least-privilege access, to limit the impact of compromised credentials and increase the chance of detecting anomalous activity.
Focus on mitigating insider threats, a practice that can help limit malicious actions not only by employees but also by external actors (who, after all, appear to be insiders once they've gained access).
Conduct regular threat hunting, which can help detect fileless attacks and threat actors working to evade your defenses early.
Attackers are always looking for new ways to infiltrate organizations' systems, and the new ploys we're seeing certainly add to the advantages cybercriminals have over organizations that are unprepared for attacks. However, organizations are far from helpless. By taking the practical and proven steps outlined in this article, organizations can make life very tough for IABs and ransomware groups, despite their new array of tactics.
About the Author(s)
You May Also Like
The fuel in the new AI race: Data
April 23, 2024Securing Code in the Age of AI
April 24, 2024Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




