It's difficult to stop supply chain attacks if partner accounts are compromised. What can you do when these attacks are indistinguishable from insider threats?
The current rash of financial fraud and supply chain attacks exploit a seemingly unsolvable vulnerability in your security strategy. Attackers exploit the fact that you must communicate with outside partners and vendors to thrive as a company or an institution. As you interact with partners, the door to exploitation opens, specifically in the form of supply chain attacks. These attacks are tremendously hard to detect since malware and malicious links are not necessary for successful exfiltration, so the final "kill shot" has the most subtle of fingerprints. Yet efficacy is so high, in just the first few months of 2021, such attacks have succeeded in millions of dollars in currency theft and incalculable troves of stolen data.
Compromised credentials are the key to the attacker's success. But here is what's disturbing. It is not your credentials that are the linchpin in stealing from you. The bad actor lurks while legitimate trust is built between you and a partner. No malware is delivered. No network penetration is involved. Yet the theft succeeds.
Often, the supply chain attack involves a business email compromise (BEC) exploiting invoice fraud. Detecting the final diversion of funds that comes from an established trusted vendor, involving a long legitimate email thread, and using a perfectly altered invoice is difficult to detect. What are the strategies to stop these attacks?
Strong security solutions extend the concept of "zero trust" beyond its original premise of micro-segmentation and incorporate that idea of reducing trust for your most trusted communications. While seemingly ironic, the point is, the more you trust a person, entity, or a communication, the more successful an attack that exploits it can be.
So, how do you apply the concept of zero trust to partner interactions and prevent supply chain-based attacks? Effective zero-trust application must start at the point where your own infrastructure and control begins: email.
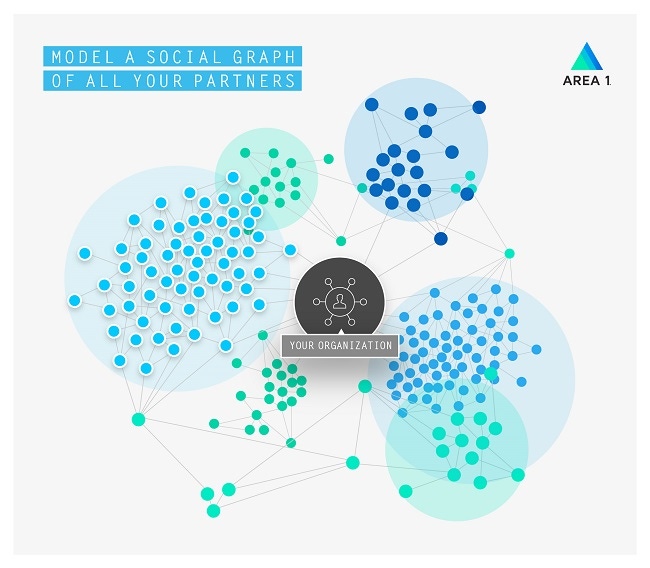
To extend zero trust to email, consider the notion of a social graph:
Your graph extends to everyone you interact with, not just employees in your own organization. This means your risk surface area is much larger than it initially appears when interactions are considered across multiple parties and systems.

Think of each interaction as a microsegment in the zero-trust world that must be "authenticated." There should be no implied trust between parties, regardless of how often you have communicated, since you do not know if a partner's account has been compromised.
To apply the concepts of zero trust to detect supply chain phishing and compromised partners in email, consider the following three factors.
Campaign Source
An email-based attack can leave subtle clues about the attack or attacker. Beyond looking at the sender information for spoofed names or domains, inspecting the sending infrastructure and source of an email can help identify whether it's malicious.
For example, if there are links or nested links within the email, where are they being hosted? Is the sender domain a legitimate organization's domain or does it use a newly created webmail domain from Microsoft 365 or Gmail? In our Office 365 missed threats report, nearly half (48.9%) of missed threats were from recently created domains.
Attackers tend to reuse hosting infrastructure and spin up new domains. By tracking attacker infrastructure, phish can be linked to an attacker even if accounts and domains have no known reputation. Preemptive, in-the-wild crawling and indexing also allow you to discover new malicious infrastructure quicker.
Message Sentiment and Conversational Context
Some attacks like BEC don't contain malicious links or documents. Instead, they rely on social engineering to trick unsuspecting users into sending funds or disclosing sensitive information, often by spoofing a trusted party like an internal employee or executive. Specific types of BEC based on supply chain compromises are the most difficult to detect since the target victim organization typically doesn't know a supplier's account has been compromised.
Detecting these types of malware-less attacks requires detailed analysis of message sentiment and conversational context. You need to understand what is actually being expressed within a message, or its intent. Detecting variations within message threads is also important to surface attempted fraud. Since supply chain BEC attacks can take place over weeks and months, it is important to be able to consider variations in behavior and requests over extended periods of time.
Partner Social Graph
Just as each organization has a social graph of interactions, each supplier also has theirs. Evidence of vendor account takeovers can be surfaced by properly assessing each supply chain partner's reputation and their partners' reputation. This, along with taking into account message sentiment and conversation context mentioned before, can signal whether a known contact's account has been compromised.
Supply chain attacks complicate detections by making everyone an insider. By applying zero-trust principles to email, the source of most phishing and account takeover attempts, organizations stand a better chance of early detection and minimized damages.
To learn more, check out the following resources, and get an assessment of your current risk from partner-originated email attacks:
 About the Author
About the Author
Before joining Area 1 Security as CEO and president in 2020, Patrick Sweeney served as CEO of Talari Networks, where he reinvigorated the company's market leadership and completed the successful sale of the company to Oracle, Inc. Before Talari/Oracle, from 2001-2017, Patrick played key executive management roles in taking SonicWall private under Thoma Bravo; the acquisition of SonicWall by Dell Inc., and the divestiture of SonicWall to Francisco Partners. While at Dell Inc., Patrick served as vice president for the Dell Security Group and Dell Software Group.
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




