Button for reporting suspicious emails to the security team works with Microsoft's email software.
You can school users over and over on what to do and not to do with suspicious emails, but that doesn't mean they always take the proper action. A new free add-in for Microsoft Outlook aims to simplify some of that process for enterprises for reporting a suspicious email.
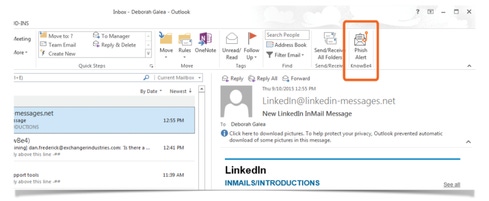
Security awareness training firm KnowBe4 this month will roll out the freebie Phish Alert button add-in for Outlook in the first quarter of 2016. "The moment a user sees [an email] that is a red flag, they just click on the Phish Alert button and that allows the security team to pick it up," says Stu Sjouwerman, CEO of KnowBe4. That eliminates any confusion of whether to delete or forward the message in question, or to call the help desk, he says.
Sjouwerman says phishing remains a major problem in the enterprise: 67% of malware infections come via email and 63% via Web attacks.
{Image 1}
About the Author(s)
You May Also Like
Beyond Spam Filters and Firewalls: Preventing Business Email Compromises in the Modern Enterprise
April 30, 2024Key Findings from the State of AppSec Report 2024
May 7, 2024Is AI Identifying Threats to Your Network?
May 14, 2024Where and Why Threat Intelligence Makes Sense for Your Enterprise Security Strategy
May 15, 2024Safeguarding Political Campaigns: Defending Against Mass Phishing Attacks
May 16, 2024
Black Hat USA - August 3-8 - Learn More
August 3, 2024Cybersecurity's Hottest New Technologies: What You Need To Know
March 21, 2024




